|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2006:098: postgresql Vulnerability Assessment Details
|
MDKSA-2006:098: postgresql |
||
|
Check for the version of the postgresql package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2006:098 (postgresql). PostgreSQL 8.1.x before 8.1.4, 8.0.x before 8.0.8, 7.4.x before 7.4.13, 7.3.x before 7.3.15, and earlier versions permits context-dependent attackers to bypass SQL injection protection methods in applications via invalid encodings of multibyte characters, aka one variant of 'Encoding-Based SQL Injection.' (CVE-2006-2313) PostgreSQL 8.1.x before 8.1.4, 8.0.x before 8.0.8, 7.4.x before 7.4.13, 7.3.x before 7.3.15, and earlier versions permits context-dependent attackers to bypass SQL injection protection methods in applications that use multibyte encodings that permit the '' (backslash) byte 0x5c to be the trailing byte of a multibyte character, such as SJIS, BIG5, GBK, GB18030, and UHC, which cannot be handled correctly by a client that does not understand multibyte encodings, aka a second variant of 'Encoding-Based SQL Injection.' NOTE: it could be argued that this is a class of issue related to interaction errors between the client and PostgreSQL, but a CVE has been assigned since PostgreSQL is treating this as a preventative measure against this class of problem. (CVE-2006-2314) Packages have been patched or updated to correct these issues. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2006:098 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Amiga 4000TX computer motherboard
$2643.23
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.32
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
TF1232: a 25MHz 68030 Amiga 1200 accelerator with 64MB RAM and FPU option
$138.11
13 Available Samsung SFD-321B Floppy Drive Modified for Commodore Amiga
$30.00
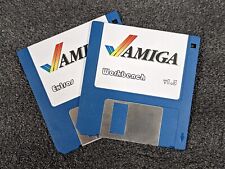
Amiga Workbench v1.3 Boot Disk + Extras A500 A2000 1.3 on DD 3.5" Floppy Disks
$14.99
Commodore Amiga A3000 Computer - WORKING - New Battery - Great Condition
$2379.15
$2.99
TF1260 including 68LC060 CPU, accelerator card for the Amiga 1200, 128MB Ram
$320.79
pi1541 Disk Emulator for Commodore -
$38.95
|
||
|
No Discussions have been posted on this vulnerability. |