|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:239: printer-filters-utils Vulnerability Assessment Details
|
MDKSA-2005:239: printer-filters-utils |
||
|
Check for the version of the printer-filters-utils package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:239 (printer-filters-utils). 'newbug' discovered a local root vulnerability in the mtink binary, which has a buffer overflow in its handling of the HOME environment variable, permiting the possibility for a local user to gain root rights. Mandriva encourages all users to upgrade immediately. The updated packages have been patched to correct these problems. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:239 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Commodore Amiga 500 Untested no power cord with mouse
$249.99
Commodore 1084S-D1 Amiga Monitor - Working
$200.00
Amiga 600 Computer * Recapped * ACA620 * 9.5MB * 8GB
$699.00
Amiga 2000 2500 Video Toaster - Card Only
$90.00
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.32
Board Master PCB Designer For Commodore Amiga
$60.00
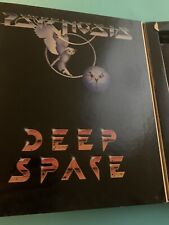
Deep Space 512K Commodore Amiga Game 3.5" 1986 Complete Very Rare Very Good Cond
$80.00
Lot of Amiga Software ✓ Imagine, Turbo Silver, ProWrite, Diskmaster ✓ 55 disks
$125.00
pi1541 Disk Emulator for Commodore -
$38.95
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
|
||
|
No Discussions have been posted on this vulnerability. |