|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:054: cyrus-sasl Vulnerability Assessment Details
|
MDKSA-2005:054: cyrus-sasl |
||
|
Check for the version of the cyrus-sasl package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:054 (cyrus-sasl). A buffer overflow was discovered in cyrus-sasl's digestmd5 code. This could lead to a remote attacker executing code in the context of the service using SASL authentication. This vulnerability was fixed upstream in version 2.1.19. The updated packages are patched to deal with this issue. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:054 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

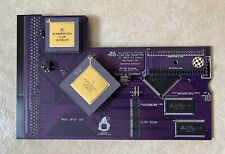
TF1232: a 50MHz 68030 Amiga 1200 accelerator with 128MB RAM, 68882 FPU + IDE
$219.22
TF330: an Amiga CD32 expansion set with 68030, 128MB RAM, IDE interface, CF card
$189.99
Commodore Amiga 500 Untested no power cord with mouse
$249.99
Terrible Fire Accelerator TF534 For AMIGA 500 2000 2500
$140.00
Amiga 2000 2500 Video Toaster - Card Only
$90.00
2 Commodore Amiga GVP TBC+'s bundled ,frame buffer&Fast Ram,Comb Filter
$360.00
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.32
Commodore Amiga Keyboard For Parts Repair Untested & Incomplete
$100.00
pi1541 Disk Emulator for Commodore -
$38.95
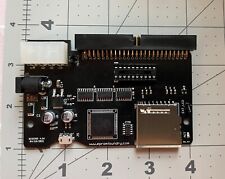
SCSI2SD for Audio Samplers, Amiga, Mac, PC - USA Made&Sold
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |