|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2004:008: tcpdump Vulnerability Assessment Details
|
MDKSA-2004:008: tcpdump |
||
|
Check for the version of the tcpdump package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2004:008 (tcpdump). A number of vulnerabilities were discovered in tcpdump versions prior to 3.8.1 that, if fed a maliciously crafted packet, could be exploited to crash tcpdump or potentially execute arbitrary code with the rights of the user running tcpdump. These vulnerabilities include: An infinite loop and memory consumption processing L2TP packets (CVE-2003-1029). Infinite loops in processing ISAKMP packets (CVE-2003-0989, CVE-2004-0057). A segmentation fault caused by a RADIUS attribute with a large length value (CVE-2004-0055). The updated packages are patched to correct these problem. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2004:008 Network Security Threat Level: High Networks Security ID: 9263, 9423 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Apple Lisa Replica Desktop Mouse | M0100 | Mac Plus | 128k | 512k |
$300.00
Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
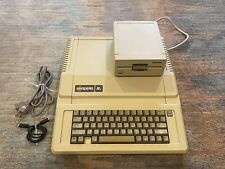
Apple IIe Computer - 128k Enhanced w/ 80col + 5.25 Drive Card
$249.00
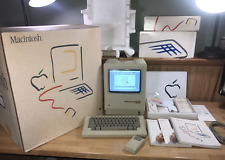
1984 APPLE MACINTOSH 128K 40th Anniversary MATCHING # BOX Set 1st Mac M0001 NICE
$7499.99
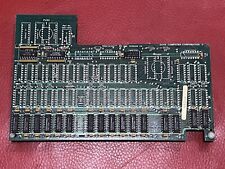
RARE Dove Computer MACSNAP Memory Upgrade for Apple Macintosh 128K 512K Computer
$159.99
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$349.00
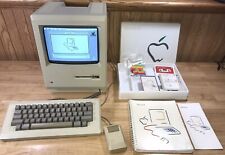
1984 APPLE MACINTOSH Model M0001 1st MAC 128K 40th Anniversary PICASSO KIT NICE
$4499.99
Apple Macintosh Mac 128K M0001 Computer 1984 w/Keyboard M0110 Mouse M0100 & Bag
$849.99
Apple M0120 Keypad Keyboard for Macintosh 128k 512k Plus - FULLY TESTED
$99.99
Apple Macintosh 128K Parts Kit - P/N 073-0140-A
$273.60
|
||
|
No Discussions have been posted on this vulnerability. |