|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1134] DSA-1134-1 mozilla-thunderbird Vulnerability Assessment Details
|
[DSA1134] DSA-1134-1 mozilla-thunderbird |
||
|
DSA-1134-1 mozilla-thunderbird Detailed Explanation for this Vulnerability Assessment Several security related problems have been discovered in Mozilla which are also present in Mozilla Thunderbird. The Common Vulnerabilities and Exposures project identifies the following vulnerabilities: Eric Foley discovered that a user can be tricked to expose a local file to a remote attacker by displaying a local file as image in connection with other vulnerabilities. [MFSA-2006-39] XUL attributes are associated with the wrong URL under certain circumstances, which might permit remote attackers to bypass restrictions. [MFSA-2006-35] Paul Nickerson discovered that content-defined setters on an object prototype were getting called by privileged user interface code, and "moz_bug_r_a4" demonstrated that the higher privilege level could be passed along to the content-defined attack code. [MFSA-2006-37] A vulnerability permits remote attackers to execute arbitrary code and create notifications that are executed in a privileged context. [MFSA-2006-43] Mikolaj Habryn discovered a buffer overflow in the crypto.signText function that permits remote attackers to execute arbitrary code via certain optional Certificate Authority name arguments. [MFSA-2006-38] Mozilla team members discovered several crashes during testing of the browser engine showing evidence of memory corruption which may also lead to the execution of arbitrary code. This problem has only partially been corrected. [MFSA-2006-32] An integer overflow permits remote attackers to cause a denial of service and may permit the execution of arbitrary code. [MFSA-2006-32] Masatoshi Kimura discovered a double-free vulnerability that permits remote attackers to cause a denial of service and possibly execute arbitrary code via a VCard. [MFSA-2006-40] Chuck McAuley discovered that a text input box can be pre-filled with a filename and then turned into a file-upload control, permiting a malicious website to steal any local file whose name they can guess. [MFSA-2006-41, MFSA-2006-23, CVE-2006-1729] Masatoshi Kimura discovered that the Unicode Byte-order-Mark (BOM) is stripped from UTF-8 pages during the conversion to Unicode before the parser sees the web page, which permits remote attackers to conduct cross-site scripting (XSS) attacks. [MFSA-2006-42] Paul Nickerson discovered that the fix for CVE-2005-0752 can be bypassed using nested javascript: URLs, permiting the attacker to execute privileged code. [MFSA-2005-34, MFSA-2006-36] Paul Nickerson demonstrated that if a possible hacker could convince a user to right-click on a broken image and choose "View Image" from the context menu then he could get JavaScript to run. [MFSA-2006-34] Kazuho Oku discovered that Mozilla's lenient handling of HTTP header syntax may permit remote attackers to trick the browser to interpret certain responses as if they were responses from two different sites. [MFSA-2006-33] The Mozilla researcher "moz_bug_r_a4" discovered that JavaScri [...] Solution : http://www.debian.org/security/2006/dsa-1134 Network Security Threat Level: High Networks Security ID: 18228 Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

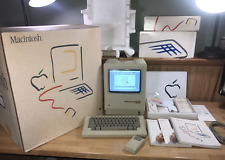
Macintosh Platinum Mouse - Apple 128K 512K 512Ke Mac Plus Lisa IIe M0100 - NEW
$44.99
1984 APPLE MACINTOSH 128K 40th Anniversary MATCHING # BOX Set 1st Mac M0001 NICE
$7999.99
Apple Macintosh 128k 512k Plus Analog Board Capacitor Re-Cap Kit - US Shipping
$23.95
Macintosh Platinum Mouse - Apple II, IIe, 128K 512K 512Ke Mac Plus M0100 - New
$35.99
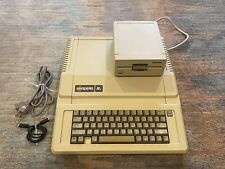
Vintage Apple lle 128k Enhanced Computer A2S2064 Rebuilt W/ Disk Drive & more
$359.99
Apple Macintosh M0001 128K computer & M0110 keyboard/mouse, for parts/repair
$300.00
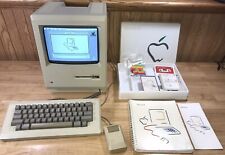
1984 APPLE MACINTOSH Model M0001 1st MAC 128K 40th Anniversary PICASSO KIT NICE
$4999.99
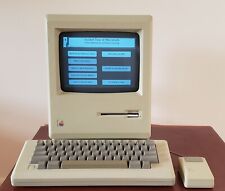
Working 1984 Apple Mac Macintosh 128K M0001 - Restored/Serviced/Tested
$1386.20
Apple Macintosh 128K M0001 Computer with 128K Label - Estate Sale SOLD AS IS
$2468.10
Apple M0120 Keypad Keyboard for Macintosh 128k 512k Plus - FULLY TESTED
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |