|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain a shell remotely >> Apache < 2.0.44 DOS device name Vulnerability Assessment Details
|
Apache < 2.0.44 DOS device name |
||
|
Checks for version of Apache Detailed Explanation for this Vulnerability Assessment The remote host appears to be running a version of Apache for Windows which is older than 2.0.44 There are several flaws in this version which permit a possible hacker to crash this host or even execute arbitrary code remotely, but it only affects WindowsME and Windows9x *** Note that Nessus solely relied on the version number *** of the remote server to issue this warning. This might *** be a false positive Solution : Upgrade to version 2.0.44 See also : http://www.apache.org/dist/httpd/Announcement.html Network Security Threat Level: High Networks Security ID: 6659 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Renaud Deraison |
||
|
Cables, Connectors |

Vintage INTEL PENTIUM PRO -Gold CPU
$45.00
Vintage Apple Macintosh Keyboard M0116 + ADB Mouse G5431
$85.00
Vintage Microsoft Office 2000 Premium 4 CDs + Product Keys + Service Pack CD
$59.99
Vintage Intel UPI-41 Universal Peripheral Interface User's Manual
$24.99
ISA Video Card, WD90C31A-LR, 1mb (WDXLR83160) Vintage/ Retro Gaming
$79.99
VINTAGE DEC DIGITAL DISK FOR RK 05 HARD DRIVE / DECPACK 2200 BPI-16
$95.00
Vintage 1991 Hewlett Packard DeskJet 500 Printer Manual Bundle W Floppy Disk
$23.99
Vintage -The Applesoft Tutorial Apple II Basic Programming Manual--Paperback
$19.99
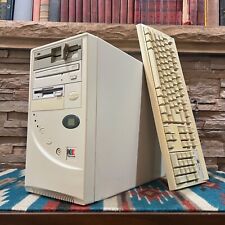
Vintage Retro AT PC Tower - Pentium MMX 166 24MB 3.5 5.25" Sound Keyboard POSTS
$199.00
Vintage 1989 Macintosh Adobe Type Manager User Guide
$30.00
|
||
|
No Discussions have been posted on this vulnerability. |