|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2005:067: kernel Vulnerability Assessment Details
|
SUSE-SA:2005:067: kernel |
||
|
Check for the version of the kernel package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2005:067 (kernel). This kernel update for SUSE Linux 10.0 contains fixes for XEN, various security fixes and bug fixes. This update includes a more recent snapshot of the upcoming XEN 3.0. Many bugs have been fixed. Stability for x86_64 has been improved. Stability has been improved for SMP, and now both i586 and x86_64 kernels are built with SMP support. It also contains several security fixes : - CVE-2005-3783: A check in ptrace(2) handling that finds out if a process is attaching to itself was incorrect and could be used by a local attacker to crash the machine. - CVE-2005-3784: A check in reaping of terminating child processes did not consider ptrace(2) attached processes and would leave a ptrace reference dangling. This could lead to a local user being able to crash the machine. - CVE-2005-3271: A task leak problem when releasing POSIX timers was fixed. This could lead to local users causing a local denial of service by exhausting system memory. - CVE-2005-3805: A locking problem in POSIX timer handling could be used by a local attacker on a SMP system to deadlock the machine. - CVE-2005-3181: A problem in the Linux auditing code could lead to a memory leak which finally could exhaust system memory of a machine. - CVE-2005-2973: An infinite loop in the IPv6 UDP loopback handling can be easily triggered by a local user and lead to a denial of service. - CVE-2005-3806: A bug in IPv6 flow label handling code could be used by a local attacker to free non-allocated memory and in turn corrupt kernel memory and likely crash the machine. - CVE-2005-3807: A memory kernel leak in VFS lease handling can exhaust the machine memory and so cause a local denial of service. This is seen in regular Samba use and could also be triggered by local attackers. - CVE-2005-3055: Unplugging an user space controlled USB device with an URB pending in user space could crash the kernel. This can be easily triggered by local attacker. - CVE-2005-3180: Fixed incorrect padding in Orinoco wireless driver, which could expose kernel data to the air. - CVE-2005-3044: Missing sockfd_put() calls in routing_ioctl() leaked file handles which in turn could exhaust system memory. - CVE-2005-3527: A race condition in do_coredump in signal.c permits local users to cause a denial of service (machine hang) by triggering a core dump in one thread while another thread has a pending SIGSTOP. Solution : http://www.suse.de/security/advisories/2005_67_kernel.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

MITS Altair 8800 Computer Bamboo Reproduction Arduino Tested Working Assembled
$649.99
Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS ALTAIR 8800 88-2SIO S-100 Reproduction Board
$35.00
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
Altair MITS 8800 CPU Parts Kit not IMSAI 8080 S100 (board NOT included)
$64.95
$22.50
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
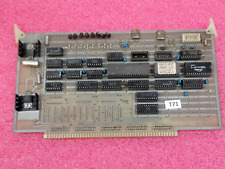
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
VINTAGE DEC 1975 VOL 1 ISSUE 1 SCCS INTERFACE MAGAZINE MITS ALTAIR COVER & ADS
$359.99
|
||
|
No Discussions have been posted on this vulnerability. |