|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2005:050: kernel Vulnerability Assessment Details
|
SUSE-SA:2005:050: kernel |
||
|
Check for the version of the kernel package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2005:050 (kernel). The Linux kernel was updated to fix the following security issues: - CVE-2005-2457: A problem in decompression of files on 'zisofs' filesystem was fixed. - CVE-2005-2458: A potential buffer overflow in the zlib decompression handling in the kernel was fixed. - CVE-2005-2459: Some return codes in zlib decoding were fixed which could have led to a possible hacker crashing the kernel. - CVE-2005-2555: Only processes with the CAP_NET_ADMIN capability is now permited load socket policies. - CVE-2005-2456: Fixed a potential overflow caused by missing boundary checks of sock->sk_policy in net/xfrm/. - AMD64/EM64T/x86_64 only: A previous fix for a denial of service attack with compat 32bit mode programs was too strict and could crash the kernel. (The earlier fix had the Mitre CVE ID CVE-2005-1765.) - S/390 only: Fixed /sys/ permissions where a user could change machine states, including powering down or up partitions. - CVE-2005-0916: PowerPC only: A missing patch for a hugetlb memory context handling problem was added. Above problems affect SUSE Linux 9.1 up to 9.3 and SUSE Linux Enterprise Server 9. Solution : http://www.suse.de/security/advisories/2005_50_kernel.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
***NEW*** BCM RX67Q mATX Gaming Motherboard Combo | Intel i5-3470 | 16GB DDR3
$49.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.42
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
Gigabyte GA-B75M-HD3 Intel LGA1155 DDR3 Desktop Motherboard MicroATX USB 3.0
$26.99
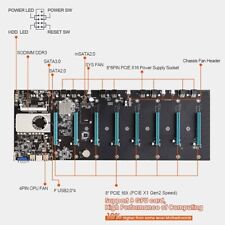
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
GIGABYTE Z690 AORUS Elite AX (LGA 1700/Intel 7690/WiFi 6) - Gaming Motherboard
$99.86
|
||
|
No Discussions have been posted on this vulnerability. |