|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> yppasswdd overflow Vulnerability Assessment Details
|
yppasswdd overflow |
||
|
heap overflow through yppasswdd Detailed Explanation for this Vulnerability Assessment The remote RPC service 100009 (yppasswdd) is vulnerable to a buffer overflow which permits any user to obtain a root shell on this host. Solution : disable this service if you don't use it, or contact Sun for a patch Network Security Threat Level: High Networks Security ID: 2763 Vulnerability Assessment Copyright: This script is Copyright (C) 2001 Renaud Deraison |
||
|
Cables, Connectors |

Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
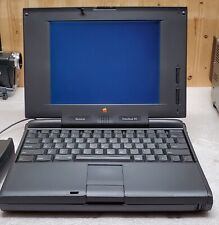
Vintage Apple Macintosh Powerbook 190 Series M3047 Laptop Parts/Repair
$69.00
Vintage Apple LisaDraw Brochure, very nice condition
$40.00
Vintage Apple Macintosh PowerBook 100 AC Power Adapter M5651 (APS-20U) | AP45
$16.99
Vintage Apple Design Powered Speakers Model M6082 by Apple Inc. - Tested Working
$70.00
Vintage Apple Macintosh II 2 M5000 Computer no power very nice w drives card
$350.00
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
VINTAGE APPLE MACINTOSH IIci DESKTOP COMPUTER - POWERS ON NO FURTHER TESTING
$149.99
MacEffects Gray ALPS Mechanical Keyboard for Vintage Apple IIe Computers
$195.00
|
||
|
No Discussions have been posted on this vulnerability. |