|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> ustorekeeper file reading Vulnerability Assessment Details
|
ustorekeeper file reading |
||
|
Searches for the existence of ustorekeeper.pl Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a CGI script that permits reading arbitrary files. Description : The 'ustorekeeper.pl' CGI script installed on the remote host permits a possible hacker to read arbitrary files subject to the rights of the http daemon (usually root or nobody). See also : http://marc.theaimsgroup.com/?l=bugtraq&m=98633176230748&w=2 Solution : Remove the CGI script. Network Security Threat Level: Medium / CVSS Base Score : 4 (AV:R/AC:L/Au:NR/C:P/A:N/I:N/B:C) Networks Security ID: 2536 Vulnerability Assessment Copyright: This script is Copyright (C) 2001 Renaud Deraison |
||
|
Cables, Connectors |

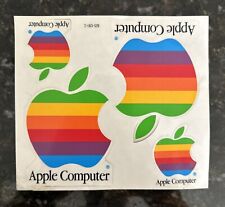
Vintage Apple Computers rainbow sticker sheet
$7.95
3DForce B-16 Vga Video Card Vintage Computer 82088C/V1
$19.00
Commodore 64 Keyboard Authentic Vintage Parts only Untested no missing keys
$45.00
NEW Manufacture OLD STYLE Oval 3 Prong Power Cord HP style 125V 7A 875W Vintage
$39.95
Apple M0116 Vintage Keyboard( Mouse + Cord )
$99.99
Vintage Atari 1025 Dot Matrix Printer - Untested - For Parts/Repair Only
$59.95
Vintage Flip 'N' File 5.25" Floppy Disk Storage Box Case with dividers
$12.00
SMC 60-600528-001 REV B Vintage Computer Card
$22.00
Vintage Enlight Beige Tower ATX Case for Retro PC/Sleeper
$69.99
Gateway 2000 EV-500-069EV CRT Computer Monitor Vintage Retro Gaming
$34.99
|
||
|
No Discussions have been posted on this vulnerability. |