|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Misc. >> qpopper options buffer overflow Vulnerability Assessment Details
|
qpopper options buffer overflow |
||
|
qpopper options buffer overflow Detailed Explanation for this Vulnerability Assessment The remote qpopper server, according to its banner, is running version 4.0.3 or version 4.0.4. These versions are vulnerable to a buffer overflow if they are configured to permit the processing of a user's ~/.qpopper-options file. A local user can cause a buffer overflow by setting the bulldir variable to something longer than 256 characters. *** This test could not confirm the existence of the *** problem - it relied on the banner being returned. Solution : Upgrade to the latest version, or disable processing of user option files. Network Security Threat Level: High Networks Security ID: 2811 Vulnerability Assessment Copyright: This script is Copyright (C) 2002 Thomas Reinke |
||
|
Cables, Connectors |

Juniper Networks EX3300 EX3300-48P 48-Port Gigabit PoE+ Switch
$40.12
Juniper Networks EX2300-C 12-Port 2XSFP Uplinks PoE+ Switch P/N: EX2300-C-12P
$299.99
JUNIPER EX3400-48P 48x 1GB PoE+ RJ-45 4x 10GB SFP+ 2x 40GB QSFP+, DUAL AC POWER
$210.00
Juniper Networks EX4300-48T 48 Port Gigabit 4 QSFP 40G 2xPSU AFO Network Switch
$89.00
Juniper Networks EX3300-24P | 24 Port Gigabit Network Switch w/ Power cord
$53.99
Juniper EX3400-48P 48-Ports PoE+ 4x SFP+ and 2x QSFP+ Managed Switch Tested
$205.00
Juniper EX4600-40F-AFI 24 SFP+/SFP Ports 4 QSFP+ Ports Dual AC Switch
$999.00
JUNIPER EX3300-48T 48 PORT SWITCH TESTED & RESET w/ Rack Ears
$49.99
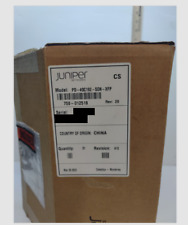
Juniper PD-4OC192-SON-XFP 710-013264 Four line-rate OC-192c/ STM-64 IPUIA01MTA
$600.00
New Factory Sealed Juniper EX2300-48P Networks 48-Port Managed Ethernet Sealed
$499.00
|
||
|
No Discussions have been posted on this vulnerability. |