|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Gain root remotely >> qpopper buffer overflow Vulnerability Assessment Details
|
qpopper buffer overflow |
||
|
qpopper buffer overflow Detailed Explanation for this Vulnerability Assessment There is a bug in some versions of qpopper which permit a remote user to become root using a buffer overflow. Solution : upgrade to the latest version. Network Security Threat Level: High Networks Security ID: 133 Vulnerability Assessment Copyright: This script is Copyright (C) 1999 Renaud Deraison |
||
|
Cables, Connectors |

Rare Vintage Collectible Original Atari 800 Home Computer With Case - UNTESTED
$219.99
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
Vintage Atari 800XL Computer With Original Box
$140.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari Mega STE or TT Keyboard. Used. Untested.
$300.00
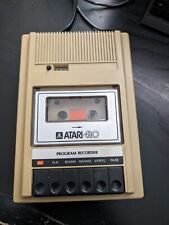
Atari 410 Program Cassette Recorder Clean Tested for power/4 cassettes/Cover
$22.99
Atari 850 Interface Module w/Power Supply and Manual Tested Works
$50.00
ATARI Home Computers HOME FILING MANAGER Software **SEALED NEW** 1982
$25.00
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
|
||
|
No Discussions have been posted on this vulnerability. |