|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Web Servers >> mod_frontpage installed Vulnerability Assessment Details
|
mod_frontpage installed |
||
|
Searches for the existence of mod_frontpage Detailed Explanation for this Vulnerability Assessment The remote host is using the Apache mod_frontpage module. mod_frontpage older than 1.6.1 is vulnerable to a buffer overflow which may permit a possible hacker to gain root access. *** Since Nessus was not able to remotely acertain the version *** of mod_frontage you are running, you are advised to manually *** check which version you are running as this might be a false *** positive. If you want the remote server to be remotely secure, we advise you do not use this module at all. Solution : Disable this module Network Security Threat Level: High Networks Security ID: 4251 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Renaud Deraison |
||
|
Cables, Connectors |

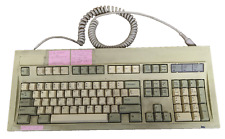
Vintage Keytronic PC/AT VT Switch FCC ID:CIG8AVE03435 TESTED WORKING
$30.00
NMB KEYBOARD RT2258TW NMB PS/2 BEIGE 121944-101 REV A VINTAGE NEW OLD STOCK
$25.99
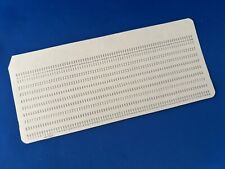
Lot Of 5 - Vintage IBM style 80 Column Punch Cards - Kelly 5081, Pink Print Band
$5.00
Vintage Dream Writer NTS 325 Computer Basic Language Notebook “Untested “
$30.00
Vintage Nan Tan KB-6251EA Mechanical Keyboard Rare
$29.99
Vintage IBM 80 Character Punch Card 5081 Unpunched & Non-Vintage Code Tutorial
$3.99
Vintage Sharp CE-126P Printer & Cassette interface, USA Seller
$50.00
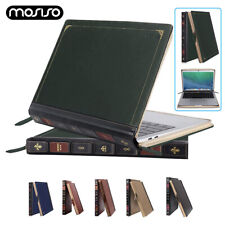
PU Leather Laptop Sleeve Case for MacBook Air Pro 13 14 15 16 inch Vintage Cover
$28.99
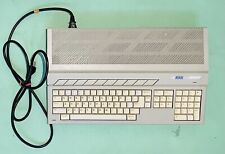
Vintage Atari 1040STf Computer with Mouse and Box, Minimal Testing, Pls Read
$149.99
Vintage Nan Tan KB-5161 Clicky Mechanical Alps Keyboard Blue **Arabic Key**
$130.00
|
||
|
No Discussions have been posted on this vulnerability. |