|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Useless services >> X Display Manager Control Protocol (XDMCP) Vulnerability Assessment Details
|
X Display Manager Control Protocol (XDMCP) |
||
|
Checks if XDM has XDMCP protocol enabled Detailed Explanation for this Vulnerability Assessment Summary : XDMCP is running on the remote host. Description : XDMCP permit a Unix user to remotely obtain a graphical X11 login (and therefore act as a local user on the remote host). If a possible hacker gains a valid login and password, he may be able to use this service to gain further access on the remote host. A possible hacker may also use this service to mount a dictionary attack against the remote host to try to log in remotely. Note that XDMCP (the Remote Desktop Protocol) is vulnerable to Man-in-the-middle attacks, making it easy for attackers to steal the credentials of legitimates users by impersonating the XDMCP server. In addition to this, XDMCP is not a ciphered protocol which make it easy for a possible hacker to capture the keystrokes entered by the user. Solution : Disable the XDMCP if you do not use it, and do not permit this service to run across the internet Network Security Threat Level: Low / CVSS Base Score : 1.9 (AV:R/AC:H/Au:NR/C:P/I:N/A:N/B:N) Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2002 Pasi Eronen |
||
|
Cables, Connectors |

Apple Xserve A1009 14-Bay RAID Network Storage Array Enclosure
$249.99
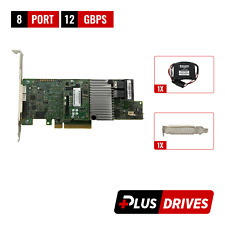
Oracle 7085209 LSI MegaRAID SAS 9361-8i 1GB Cache 12Gbps SAS/SATA PCIe RAID Card
$28.20
DELL 4Y5H1 PERC H330 12GB SAS 6GB SATA PCI-E RAID CONTROLLER CARD
$38.49
Broadcom LSI 9400-16i Raid card SAS/SATA/NVME SFF-8643 SAS3416 PCIe 3.1 x8 HBA
$154.96
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$86.99
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
Dell PERC H330 PCIe 3.0 x8 RAID Storage Controller 04Y5H1 High Profile
$14.99
Lenovo 930-16i PCIe SAS RAID Controller FRU P/N: 01KN508 Tested Working
$149.99
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
|
||
|
No Discussions have been posted on this vulnerability. |