|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows : User management >> Users information : Never changed password Vulnerability Assessment Details
|
Users information : Never changed password |
||
|
Lists the users that have special privileges Detailed Explanation for this Vulnerability Assessment Summary : It is possible to retrieve users who can never changed their password using the supplied credentials. Description : Using the supplied credentials it was possible to extract the list of domain users who never changed their password. It is recommended to permit/force users to change their password for security reasons. Network Security Threat Level: Medium / CVSS Base Score : 4 (AV:R/AC:L/Au:NR/C:P/A:N/I:N/B:C) Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

Extron RGB-160XI Analog Computer Video 60-378-01
$187.06
NEC Multisync II JC-1402HMA VGA EGA CGA Analog TTL Computer Monitor Vintage 1988
$699.99
Vintage 1960s Donner Model 3000 Analog Computer ~ MUSEUM PIECE Extremely Rare
$4000.00
NEW Aquarius+ Computer Signature Edition - 8Bit Retro System
$239.00
Apple Macintosh SE/30 M5119 Computer 8MB RAM Recapped Working *See Description*
$450.00
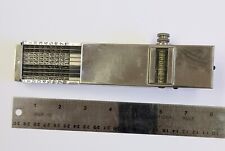
Landen Computer. Circa 1898. the Rapid Computer Company. With Original Case.
$425.00
IBM Modem Saver Phone Line Tester
$7.99
Burr Brown Analog Computer parts Circuit boards w Helipot Potentiometers 1631a
$85.00
Sony Trinitron CPD-1304 9 PIN Analog Vintage CRT Monitor - Great for Retro PC
$475.30
Wooting Two HE Mechanical Keyboard Analog Linear Lekker Switches
$299.99
|
||
|
No Discussions have been posted on this vulnerability. |