|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN77-1 : squid vulnerabilities Vulnerability Assessment Details
|
USN77-1 : squid vulnerabilities |
||
|
squid vulnerabilities Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - squid - squid-cgi - squid-common - squidclient Description : A possible authentication bypass was discovered in the LDAP authentication backend. LDAP ignores leading and trailing whitespace in search filters. This could possibly be abused to bypass explicit access controls or confuse accounting when using several variants of the login name. (CVE-2005-0173) Previous Squid versions were not strict enough while parsing HTTP requests and responses. Various violations of the HTTP protocol, such as multiple Content-Length header lines, invalid "Carriage Return" characters, and HTTP header names containing whitespace, led to cache pollution and could possibly be exploited to deliver wrong content to clients. (CVE-2005-0174) Squid was susceptible to a cache poisoning attack called "HTTP response splitting", where false replies are injected in the HTTP stream. This permited malicious web servers to forge wrong cache content for arbitrary web sites, which was then delivered to Squid clients. (CVE-2005-0175) The FSC Vulnerability Research Team discovered a buffer overflow in t [...] Solution : Upgrade to : - squid-2.5.5-6ubuntu0.4 (Ubuntu 4.10) - squid-cgi-2.5.5-6ubuntu0.4 (Ubuntu 4.10) - squid-common-2.5.5-6ubuntu0.4 (Ubuntu 4.10) - squidclient-2.5.5-6ubuntu0.4 (Ubuntu 4.10) Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
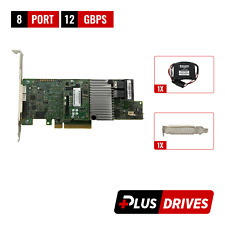
Cables, Connectors |

LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
Dell R630 8SFF 2.4Ghz 12-Core 128GB H330 RAID 10GB RJ-45 NIC 2x750W PSU 8x Trays
$430.04
Dell R630 8SFF 2.4Ghz 20-Core 128GB H730 RAID 10GB RJ-45 NIC 2x750W PSU 8x Trays
$455.04
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
NEW LSI MEGARAID SAS 9361-8i 12GB/s SAS + SATA RAID CONTROLLER CARD PCIe x8 3.0
$99.00
Yottamaster 4Bay RAID RGB Hard Drive Enclosure Type B Fr 2.5'' 3.5" SATA HDD SSD
$149.99
|
||
|
No Discussions have been posted on this vulnerability. |