|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN73-1 : python2.2, python2.3 vulnerability Vulnerability Assessment Details
|
USN73-1 : python2.2, python2.3 vulnerability |
||
|
python2.2, python2.3 vulnerability Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - idle-python2.2 - idle-python2.3 - python2.2 - python2.2-dev - python2.2-doc - python2.2-examples - python2.2-gdbm - python2.2-mpz - python2.2-tk - python2.2-xmlbase - python2.3 - python2.3-dev - python2.3-doc - python2.3-examples - python2.3-gdbm - python2.3-mpz - python2.3-tk Description : The Python developers discovered a flaw in the SimpleXMLRPCServer module. Python XML-RPC servers that used the register_instance() method to register an object, but do not have a _dispatch() method, permited remote users to access or change function internals using the im_* and func_* attributes. Solution : Upgrade to : - idle-python2.2-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - idle-python2.3-2.3.4-2ubuntu0.1 (Ubuntu 4.10) - python2.2-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.2-dev-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.2-doc-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.2-examples-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.2-gdbm-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.2-mpz-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.2-tk-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.2-xmlbase-2.2.3-10ubuntu0.1 (Ubuntu 4.10) - python2.3 [...] Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

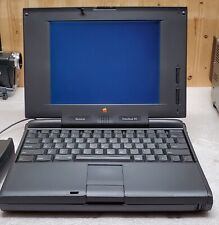
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Vintage Apple Macintosh II 2 M5000 Computer no power very nice w drives card
$350.00
Apple MacIntosh IIcx Vintage Desktop Computer M5650 - 1988/89
$200.00
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
VINTAGE REFURBISHED MACINTOSH SE WITH BLUESCSI RECAPPED POWER SUPPLY
$300.00
VINTAGE RARE POWER R 2703 VIDEO ADAPTER FOR MACINTOSH SE SE/30 LCD NOT INCLUDED
$300.00
Vintage Apple Macintosh Powerbook 190 Series M3047 Laptop Parts/Repair
$69.00
Apple Mac IIsi computer Very Good condition Vintage
$100.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
APPLE MACINTOSH PLUS M0001A Vintage Mac Computer Tested Working
$799.99
|
||
|
No Discussions have been posted on this vulnerability. |