|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN162-1 : ekg vulnerabilities Vulnerability Assessment Details
|
USN162-1 : ekg vulnerabilities |
||
|
ekg vulnerabilities Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - ekg - libgadu-dev - libgadu3 Description : Marcin Owsiany and Wojtek Kaniewski discovered that some contributed scripts (contrib/ekgh, contrib/ekgnv.sh, and contrib/getekg.sh) in the ekg package created temporary files in an insecure way, which permited exploitation of a race condition to create or overwrite files with the rights of the user invoking the script. (CVE-2005-1850) Marcin Owsiany and Wojtek Kaniewski discovered a shell command injection vulnerability in a contributed utility (contrib/scripts/ekgbot-pre1.py). By sending specially crafted content to the bot, a possible hacker could exploit this to execute arbitrary code with the rights of the user running ekgbot. (CVE-2005-1851) Marcin Ślusarz discovered an integer overflow in the Gadu library. By sending a specially crafted incoming message, a remote attacker could execute arbitrary code with the rights of the application using libgadu. (CVE-2005-1852) Eric Romang discovered that another contributed script (contrib/scripts/linki.py) created temporary files in an insecure way, whi [...] Solution : Upgrade to : - ekg-1.5-4ubuntu1.2 (Ubuntu 5.04) - libgadu-dev-1.5-4ubuntu1.2 (Ubuntu 5.04) - libgadu3-1.5-4ubuntu1.2 (Ubuntu 5.04) Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

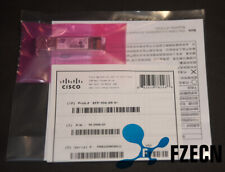
Cisco SFP-10/25G-CSR-S 10/25GBASE-CSR SFP28, 850nm, 100m, LC,
$54.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
Silicom (PE210G2SPI9A-XR) 10Gb Dual Port SFP+ PCIe Ethernet Adapter Low Profile
$19.99
Cisco GLC-GE-100FX 100BASE-FX SGMII SFP, 1310nm, 2km, LC, MMF
$83.99
Genuine Cisco SFP-10G-SR V03 10GBASE-SR SFP+ Transceiver Module 10-2415-03
$8.00
10Gtek ASF-10G-T 10GBase-T 10GbE SFP+ to RJ-45 Copper Optical Transceiver Module
$35.99
SFP-10G-SR Original Cisco 10GBASE-SR SFP+ V02 Multi mode Transceiver 10-2415-02
$5.00
NEW Sealed Cisco SFP-10G-SR-S 10G SR SFP+ Module 850nmMM *US Shipping*
$15.00
LOT OF 20 Genuine Cisco SFP-10G-SR V03 10GBASE-SR SFP+ Transceiver Module
$89.00
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
|
||
|
No Discussions have been posted on this vulnerability. |