|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Ubuntu Local Security Checks >> USN134-1 : mozilla-firefox vulnerabilities Vulnerability Assessment Details
|
USN134-1 : mozilla-firefox vulnerabilities |
||
|
mozilla-firefox vulnerabilities Detailed Explanation for this Vulnerability Assessment Summary : These remote packages are missing security patches : - mozilla-firefox - mozilla-firefox-dev - mozilla-firefox-dom-inspector - mozilla-firefox-gnome-support Description : It was discovered that a malicious website could inject arbitrary scripts into a target site by loading it into a frame and navigating back to a previous Javascript URL that contained an eval() call. This could be used to steal cookies or other confidential data from the target site. If the target site is permited to raise the install confirmation dialog in Firefox then this flaw even permited the malicious site to execute arbitrary code with the rights of the Firefox user. By default only the Mozilla Update site is permited to attempt software installation however, users can permit this for additional sites. (MFSA 2005-42) Michael Krax, Georgi Guninski, and L. David Baron found that the security checks that prevent script injection could be bypassed by wrapping a javascript: url in another pseudo-protocol like "view-source:" or "jar:". (CVE-2005-1531) A variant of the attack described in CVE-2005-1160 (see USN-124-1) was discovered. Additional checks were added to make sure Javascript eval and Script [...] Solution : Upgrade to : - mozilla-firefox-1.0.2-0ubuntu5.3 (Ubuntu 5.04) - mozilla-firefox-dev-1.0.2-0ubuntu5.3 (Ubuntu 5.04) - mozilla-firefox-dom-inspector-1.0.2-0ubuntu5.3 (Ubuntu 5.04) - mozilla-firefox-gnome-support-1.0.2-0ubuntu5.3 (Ubuntu 5.04) Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: Ubuntu Security Notice (C) 2005 Canonical, Inc. / NASL script (C) 2005 Michel Arboi |
||
|
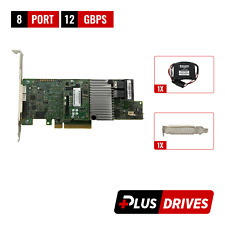
Cables, Connectors |

Oracle 7085209 LSI MegaRAID SAS 9361-8i 1GB Cache 12Gbps SAS/SATA PCIe RAID Card
$28.20
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
LSI 9207-8i 8-Port SAS Non-RAID 6GBPS PCIe Host Bus Adapter
$34.95
LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
G-Technology G-SPEED eS PRO 4-Bay Mini-SAS RAID Array 0G02057
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |