|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Tests for Nimda Worm infected HTML files Vulnerability Assessment Details
|
Tests for Nimda Worm infected HTML files |
||
|
Tests for Nimda Worm infected HTML files Detailed Explanation for this Vulnerability Assessment Your server appears to have been compromised by the Nimda mass mailing worm. It uses various known IIS vulnerabilities to compromise the server. Anyone visiting compromised Web servers will be prompted to download an .eml (Outlook Express) email file, which contains the worm as an attachment. Also, the worm will create open network shares on the infected computer, permiting access to the system. During this process the worm creates the guest account with Administrator rights. Solution: Take this server offline immediately, rebuild it and apply ALL vendor patches and security updates before reconnecting server to the internet, as well as security settings discussed in Additional Information section of Microsoft's web site at http://www.microsoft.com/technet/security/bulletin/ms01-044.mspx Check ALL of your local Microsoft based workstations for infection. Note: this worm has already infected more than 500,000 computers worldwide since its release in late 2001. See: http://www.cert.org/advisories/CA-2001-26.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2001 Matt Moore |
||
|
Cables, Connectors |

TF1230 Commodore Amiga 1200 Accelerator 50 MHz 68030 64 MB A1200 Terrible Fire
$120.00
Impulse Firecracker 24 Rev 2.1 2MB 24bit Graphics card for Amiga 2000 3000 4000
$175.00
Mini External OLED AMIGA Gotek Floppy Drive Emulator For Amiga 500/500+/600/1200
$37.41
Amiga 500 Gotek Custom Mount USB Floppy Emulator - Complete Kit with Gotek
$65.00
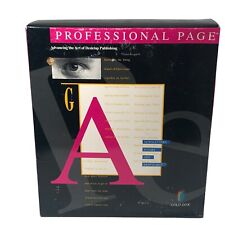
Amiga Professional Page VTG Publishing Software w/ VHS
$40.00
SIDKick Pico Commodore 64 and 128 (C64 / C128) - MOS SID 6581 / 8580 Replacement
$19.99
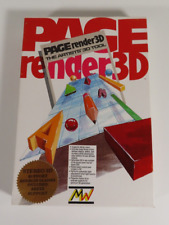
Page Render 3D Mindware Internal 3.5” Floppy Disk Amiga 500 1000 2000 Software
$44.95
Utilities Unlimited Emplant for AMIGA A2000 A3000 A4000
$475.00
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
Promqueen EPROM Programmer for Commodore VIC-20 SUPER RARE
$499.00
|
||
|
No Discussions have been posted on this vulnerability. |