|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SMTP problems >> Sendmail 'decode' flaw Vulnerability Assessment Details
|
Sendmail 'decode' flaw |
||
|
Checks if the remote mail server can be used to overwrite files Detailed Explanation for this Vulnerability Assessment The remote SMTP server seems to pipe mail sent to the 'decode' alias to a program. There have been in the past a lot of security problems regarding this, as it would permit a possible hacker to overwrite arbitrary files on the remote server. We suggest you deactivate this alias. Solution : remove the 'decode' line in /etc/aliases. Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 1999 Renaud Deraison |
||
|
Cables, Connectors |

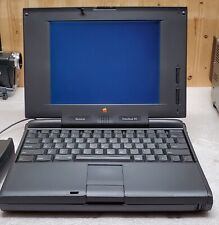
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
Vintage Apple Macintosh II 2 M5000 Computer no power very nice w drives card
$350.00
Vintage Apple Macintosh Powerbook 190 Series M3047 Laptop Parts/Repair
$69.00
Apple Mac IIsi computer Very Good condition Vintage
$100.00
VINTAGE REFURBISHED MACINTOSH SE WITH BLUESCSI RECAPPED POWER SUPPLY
$300.00
Apple Studio Display Monitor M2454 15" vintage Mac LCD
$80.00
Apple Macintosh Vintage DOS on Mac PC Compatible Interface PCI 590-4539 Y Cable
$80.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
APPLE MACINTOSH PLUS M0001A Vintage Mac Computer Tested Working
$799.99
|
||
|
No Discussions have been posted on this vulnerability. |