|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2005:016: Mozilla Firefox Vulnerability Assessment Details
|
SUSE-SA:2005:016: Mozilla Firefox |
||
|
Check for the version of the Mozilla Firefox package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2005:016 (Mozilla Firefox). This security update for Mozilla Firefox fixes following problems: - CAN-2005-0231: 'Fire tabbing' The javascript security manager usually prevents that a javascript: URL from one host is opened in a window displaying content from another host. But when the link is dropped to a tab, the security manager does not kick in. This can lead to several security problems scaling from stealing session cookies to the ability to run arbitrary code on the client system (depending on the displayed site or security settings). - CAN-2005-0232: 'Fire flashing' Using tests like Flash and the -moz-opacity filter it is possible to display the about:config site in a hidden frame or a new window. By making the user double-click at a specific screen position (e.g. using a DHTML game) you can silently toggle the status of boolean config parameters. - CAN-2005-0233: 'homograph attacks' / 'IDN cloaking' Attackers may spoof host names by using translated host name representation which look exactly the same as the original host, permiting phishing attacks or similar. We now show both IDN punycode and visible form of the host name. - CAN-2005-0255: Attackers could cause overflows or crashes in low memory situations. - Added additional Firefox bugfixes from the 1.0.1 release. Only the listed distributions are affected, others do not ship Mozilla Firefox. Also note that Firefox was called Firebird in SUSE Linux 9.0. Solution : http://www.suse.de/security/advisories/2005_16_mozilla_firefox.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
Asus H81M-C Intel LGA1150 DDR3 Desktop Motherboard MicroATX Socket H3
$24.99
MSI A320M-A PRO AM4 AMD A320 USB3.2 Gen1 Micro-ATX Motherboard
$46.99
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.42
Gigabyte GA-B75M-HD3 Intel LGA1155 DDR3 Desktop Motherboard MicroATX USB 3.0
$26.99
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
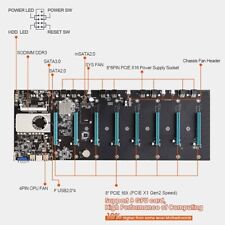
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
Asrock B550M-C Motherboard - As Is
$60.00
|
||
|
No Discussions have been posted on this vulnerability. |