|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> SuSE Local Security Checks >> SUSE-SA:2003:043: openssl Vulnerability Assessment Details
|
SUSE-SA:2003:043: openssl |
||
|
Check for the version of the openssl package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory SUSE-SA:2003:043 (openssl). OpenSSL is an implementation of the Secure Socket Layer (SSL v2/3) and Transport Layer Security (TLS v1) protocol. While checking the openssl implementation with a tool-kit from NISCC several errors were revealed most are ASN.1 encoding issues that causes a remote denial-of-service attack on the server side and possibly lead to remote command execution. There are two problems with ASN.1 encoding that can be triggered either by special ASN.1 encodings or by special ASN.1 tags. In debugging mode public key decoding errors can be ignored but also lead to a crash of the verify code if an invalid public key was received from the client. A mistake in the SSL/TLS protocol handling will make the server accept client certificates even if they are not requested. This bug makes it possible to exploit the bugs mentioned above even if client authentication is disabled. There is not other solution known to this problem then updating to the current version from our FTP servers. To make this update effective, restart all servers using openssl please. Please download the update package for your distribution and verify its integrity by the methods listed in section 3) of this announcement. Then, install the package using the command 'rpm -Fhv file.rpm' to apply the update. Solution : http://www.suse.de/security/2003_043_openssl.html Network Security Threat Level: Medium Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
Vintage Apple LisaDraw Brochure, very nice condition
$40.00
Vintage Apple Macintosh Powerbook 190 Series M3047 Laptop Parts/Repair
$69.00
Vintage Apple Macintosh PowerBook 100 AC Power Adapter M5651 (APS-20U) | AP45
$16.99
Vintage Apple Design Powered Speakers Model M6082 by Apple Inc. - Tested Working
$70.00
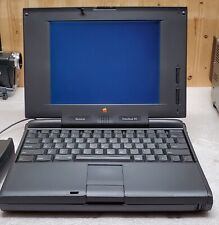
Apple Macintosh PowerBook 180 Vintage M4440 for Parts/Repair
$65.00
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
VINTAGE APPLE MACINTOSH IIci DESKTOP COMPUTER - POWERS ON NO FURTHER TESTING
$149.99
MacEffects Gray ALPS Mechanical Keyboard for Vintage Apple IIe Computers
$195.00
|
||
|
No Discussions have been posted on this vulnerability. |