|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> SAXoPRESS url Parameter Directory Traversal Vulnerability Vulnerability Assessment Details
|
SAXoPRESS url Parameter Directory Traversal Vulnerability |
||
|
Tries to retrieve a file using SAXoPRESS Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains an application that is prone to directory traversal attacks. Description : The remote host is running SAXoPRESS or Publicus, web content management systems commonly used by newspapers. The installation of SAXoPRESS / Publicus on the remote host fails to validate user input to the 'url' parameter of the 'apps/pbcs.dll' script. A possible hacker can exploit this issue to access files on the remote host via directory traversal, subject to the rights of the web server user id. See also : http://www.securityfocus.com/archive/1/430707/30/0/threaded Solution : Unknown at this time. Network Security Threat Level: High / CVSS Base Score : 7.0 (AV:R/AC:L/Au:NR/C:P/I:P/A:P/B:N) Networks Security ID: 17474 Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

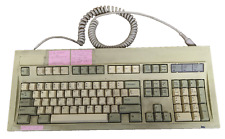
Vintage Keytronic PC/AT VT Switch FCC ID:CIG8AVE03435 TESTED WORKING
$30.00
NMB KEYBOARD RT2258TW NMB PS/2 BEIGE 121944-101 REV A VINTAGE NEW OLD STOCK
$25.99
x2 Vintage PC Accessories 3.5" Floppy Disk Holder Storage Box Case Organizer Key
$50.00
Vintage Apple MacWorld Magazine Mousepad
$15.00
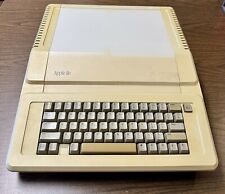
Apple IIe A2S2064 Vintage Personal Computer 128K Enhanced
$200.00
Vintage Atari 800XL Computer *UNTESTED* No Power Cords Or Cables
$50.00
Vintage Apple Support Tools Mousepad
$15.00
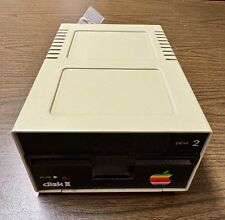
Vintage Apple Disk II 5.25" Floppy Disk Drive - Drive 2. Not Tested for Parts
$45.00
NCR Mechanical Clicky Keyboard Vintage H0150-STD1-12-17 Rare (2 Missing Keys)
$179.00
VINTAGE APPLE POWER MACINTOSH 6500/250 DESKTOP COMPUTER POWERPC BOOTS
$249.50
|
||
|
No Discussions have been posted on this vulnerability. |