|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2006-0567: php Vulnerability Assessment Details
|
RHSA-2006-0567: php |
||
|
Check for the version of the php packages Detailed Explanation for this Vulnerability Assessment Updated PHP packages that fix multiple security issues are now available for Red Hat Enterprise Linux 2.1 This update has been rated as having moderate security impact by the Red Hat Security Response Team. PHP is an HTML-embedded scripting language commonly used with the Apache HTTP Web server. A flaw was found in the zend_hash_del() PHP function. For PHP scripts that rely on the use of the unset() function, a remote attacker could force variable initialization to be bypassed. This would be a security issue particularly for installations that enable the "register_globals" setting. "register_globals" is disabled by default in Red Hat Enterprise Linux. (CVE-2006-3017) A directory traversal vulnerability was found in PHP. Local users could bypass open_basedir restrictions permiting remote attackers to create files in arbitrary directories via the tempnam() function. (CVE-2006-1494) A flaw was found in the PHP IMAP MIME header decoding function. An attacker could craft a message with an overly long header which caused PHP to crash. (CVE-2002-2214) Users of PHP should upgrade to these updated packages, which contain backported patches that resolve these issues. Solution : http://rhn.redhat.com/errata/RHSA-2006-0567.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Atari Mega STE or TT Keyboard. Used. Untested.
$300.00
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Rare Vintage Collectible Original Atari 800 Home Computer With Case - UNTESTED
$219.99
Vintage Atari 800XL Computer With Original Box
$140.00
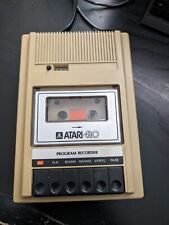
Atari 410 Program Cassette Recorder Clean Tested for power/4 cassettes/Cover
$22.99
Atari 400/800 Writing Programs 1, 2 & Biorhythm Cassettes Untested on Console
$19.95
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
Atari 400 with program recorder and manual
$199.00
|
||
|
No Discussions have been posted on this vulnerability. |