|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2006-0501: php Vulnerability Assessment Details
|
RHSA-2006-0501: php |
||
|
Check for the version of the php packages Detailed Explanation for this Vulnerability Assessment Updated PHP packages that fix multiple security issues are now available for Red Hat Enterprise Linux 2.1. This update has been rated as having moderate security impact by the Red Hat Security Response Team. PHP is an HTML-embedded scripting language commonly used with the Apache HTTP Web server. The phpinfo() PHP function did not properly sanitize long strings. An attacker could use this to perform cross-site scripting attacks against sites that have publicly-available PHP scripts that call phpinfo(). (CVE-2006-0996) The error handling output was found to not properly escape HTML output in certain cases. A possible hacker could use this flaw to perform cross-site scripting attacks against sites where both display_errors and html_errors are enabled. (CVE-2006-0208) A buffer overflow flaw was discovered in uw-imap, the University of Washington's IMAP Server. php-imap is compiled against the static c-client libraries from imap and therefore needed to be recompiled against the fixed version. (CVE-2005-2933) The wordwrap() PHP function did not properly check for integer overflow in the handling of the "break" parameter. A possible hacker who could control the string passed to the "break" parameter could cause a heap overflow. (CVE-2006-1990) Users of PHP should upgrade to these updated packages, which contain backported patches that resolve these issues. Solution : http://rhn.redhat.com/errata/RHSA-2006-0501.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

XDHXT DELL PERC H710P 6Gbps 1GB PCI RAID CONTROLLER 0XDHXT
$59.00
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$55.45
Lot of 2 -Dell P2R3R PERC H330 Mini Mono 12Gbps SAS Non-raid Controller 0P2R3R
$39.99
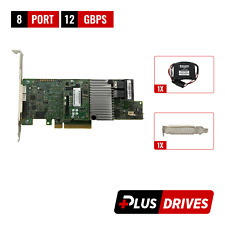
LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
Dell KMCCD PERC H730 1GB Mini Mono RAID Controller
$21.00
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
DELL PERC H310 RAID Controller with Cables, OHV52W, 6Gb/s SAS SATA PCIe x8
$19.95
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$179.99
Lenovo 930-16i PCIe SAS RAID Controller FRU P/N: 01KN508 Tested Working
$149.99
|
||
|
No Discussions have been posted on this vulnerability. |