|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2006-0101: kernel Vulnerability Assessment Details
|
RHSA-2006-0101: kernel |
||
|
Check for the version of the kernel packages Detailed Explanation for this Vulnerability Assessment Updated kernel packages that fix several security issues in the Red Hat Enterprise Linux 4 kernel are now available. This security advisory has been rated as having important security impact by the Red Hat Security Response Team. The Linux kernel handles the basic functions of the operating system. These new kernel packages contain fixes for the security issues described below: - a flaw in network IGMP processing that a permited a remote user on the local network to cause a denial of service (disabling of multicast reports) if the system is running multicast applications (CVE-2002-2185, moderate) - a flaw which permited a local user to write to firmware on read-only opened /dev/cdrom devices (CVE-2004-1190, moderate) - a flaw in gzip/zlib handling internal to the kernel that may permit a local user to cause a denial of service (crash) (CVE-2005-2458, low) - a flaw in procfs handling during unloading of modules that permited a local user to cause a denial of service or potentially gain rights (CVE-2005-2709, moderate) - a flaw in the SCSI procfs interface that permited a local user to cause a denial of service (crash) (CVE-2005-2800, moderate) - a flaw in 32-bit-compat handling of the TIOCGDEV ioctl that permited a local user to cause a denial of service (crash) (CVE-2005-3044, important) - a race condition when threads share memory mapping that permited local users to cause a denial of service (deadlock) (CVE-2005-3106, important) - a flaw when trying to mount a non-hfsplus filesystem using hfsplus that permited local users to cause a denial of service (crash) (CVE-2005-3109, moderate) - a minor info leak with the get_thread_area() syscall that permited a local user to view uninitialized kernel stack data (CVE-2005-3276, low) - a flaw in mq_open system call that permited a local user to cause a denial of service (crash) (CVE-2005-3356, important) - a flaw in set_mempolicy that permited a local user on some 64-bit architectures to cause a denial of service (crash) (CVE-2005-3358, important) - a flaw in the auto-reap of child processes that permited a local user to cause a denial of service (crash) (CVE-2005-3784, important) - a flaw in the IPv6 flowlabel code that permited a local user to cause a denial of service (crash) (CVE-2005-3806, important) - a flaw in network ICMP processing that permited a local user to cause a denial of service (memory exhaustion) (CVE-2005-3848, important) - a flaw in file lease time-out handling that permited a local user to cause a denial of service (log file overflow) (CVE-2005-3857, moderate) - a flaw in network IPv6 xfrm handling that permited a local user to cause a denial of service (memory exhaustion) (CVE-2005-3858, important) - a flaw in procfs handling that permited a local user to read kernel memory (CVE-2005-4605, important) All Red Hat Enterprise Linux 4 users are advised to upgrade their kernels to the packages associated with their machine architectures and configurations as listed in this erratum. Solution : http://rhn.redhat.com/errata/RHSA-2006-0101.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
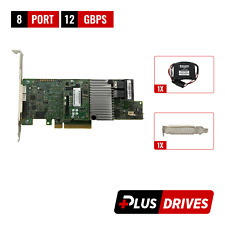
Cables, Connectors |

Adaptec ASR-81605ZQ 12G SAS 16-Port 1GB Cache PCIe x8 RAID Controller
$131.99
LSI 9207-8i 8-Port SAS Non-RAID 6GBPS PCIe Host Bus Adapter
$34.95
Oracle 7085209 LSI MegaRAID SAS 9361-8i 1GB Cache 12Gbps SAS/SATA PCIe RAID Card
$28.20
Cisco UCS LSI MegaRAID 9271CV-8I SAS2308 PCIe SAS Internal RAID Controller
$28.00
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
2 Bay RAID Hard Drive Enclosure USB 3.0 Type-B for 2.5" SATA SSD/HDD Enclosure
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |