|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2005-550: openssh Vulnerability Assessment Details
|
RHSA-2005-550: openssh |
||
|
Check for the version of the openssh packages Detailed Explanation for this Vulnerability Assessment Updated openssh packages that fix a potential security vulnerability and various other bugs are now available. This update has been rated as having low security impact by the Red Hat Security Response Team. OpenSSH is OpenBSD's SSH (Secure SHell) protocol implementation. This includes the core files necessary for both the OpenSSH client and server. A bug was found in the way the OpenSSH server handled the MaxStartups and LoginGraceTime configuration variables. A malicious user could connect to the SSH daemon in such a way that it would prevent additional logins from occuring until the malicious connections are closed. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2004-2069 to this issue. Additionally, the following issues are resolved with this update: - The -q option of the ssh client did not suppress the banner message sent by the server, which caused errors when used in scripts. - The sshd daemon failed to close the client connection if multiple X clients were forwarded over the connection and the client session exited. - The sftp client leaked memory if used for extended periods. - The sshd daemon called the PAM functions incorrectly if the user was unknown on the system. All users of openssh should upgrade to these updated packages, which contain backported patches and resolve these issues. Solution : http://rhn.redhat.com/errata/RHSA-2005-550.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
ASUS Prime Q270M-C LGA1151 DP HDMI VGA SATA 6GB/s USB 3.0 MicroATX Motherboard
$37.99
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
Gigabyte GA-B75M-HD3 Intel LGA1155 DDR3 Desktop Motherboard MicroATX USB 3.0
$26.99
NEW- ASRock B350M Motherboard (Read Description)
$60.00
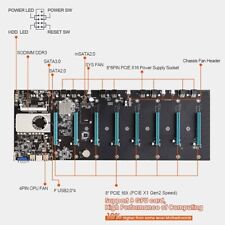
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
ASRock B250M-HDV LGA 1151 Micro ATX DDR4 Desktop Motherboard w/ IO Shield
$54.99
|
||
|
No Discussions have been posted on this vulnerability. |