|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2005-074: rsh Vulnerability Assessment Details
|
RHSA-2005-074: rsh |
||
|
Check for the version of the rsh packages Detailed Explanation for this Vulnerability Assessment Updated rsh packages that fix various bugs and a theoretical security issue are now available. This update has been rated as having low security impact by the Red Hat Security Response Team The rsh package contains a set of programs that permit users to run commands on remote machines, login to other machines, and copy files between machines, using the rsh, rlogin, and rcp commands. All three of these commands use rhosts-style authentication. The rcp protocol permits a server to instruct a client to write to arbitrary files outside of the current directory. This could potentially cause a security issue if a user uses rcp to copy files from a malicious server. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2004-0175 to this issue. These updated packages also address the following bugs: The rexec command failed with "Invalid Argument", because the code used sigaction() as an unsupported signal. The rlogind server reported "SIGCHLD set to SIG_IGN but calls wait()" message to the system log because the original BSD code was ported incorrectly to linux. The rexecd server did not function on systems where client hostnames were not in the DNS service, because server code called gethostbyaddr() for each new connection. The rcp command incorrectly used the "errno" variable and produced erroneous error messages. The rexecd command ignored settings in the /etc/security/limits file, because the PAM session was incorrectly initialized. The rexec command prompted for username and password regardless of the ~/.netrc configuration file contents. This updated package contains a patch that no longer skips the ~/.netrc file. All users of rsh should upgrade to these updated packages, which resolve these issues. Solution : http://rhn.redhat.com/errata/RHSA-2005-074.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
Gigabyte Z370P D3 ATX Z370 LGA1151 Motherboard (Support Intel 6/7th 8th 9th)
$59.99
ASUS Prime Q270M-C LGA1151 DP HDMI VGA SATA 6GB/s USB 3.0 MicroATX Motherboard
$37.99
Gigabyte GA-B75M-HD3 Intel LGA1155 DDR3 Desktop Motherboard MicroATX USB 3.0
$26.99
ASUS P8B75-M/CSM Desktop Motherboard Intel Socket LGA1155 DDR3 w/ IO
$29.99
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.31
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
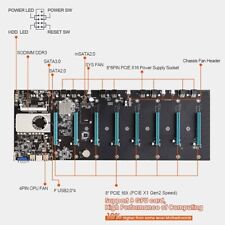
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
ASUS STRIX X299-E GAMING ATX Motherboard With I/O Shield & Intel Core i7 CPU 4.3
$189.00
|
||
|
No Discussions have been posted on this vulnerability. |