|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2004-110: galeon Vulnerability Assessment Details
|
RHSA-2004-110: galeon |
||
|
Check for the version of the galeon packages Detailed Explanation for this Vulnerability Assessment Updated Mozilla packages that fix vulnerabilities in S/MIME parsing as well as other issues and bugs are now available. Mozilla is a Web browser and mail reader, designed for standards compliance, performance and portability. Network Security Services (NSS) is a set of libraries designed to support cross-platform development of security-enabled server applications. NISCC testing of implementations of the S/MIME protocol uncovered a number of bugs in NSS versions prior to 3.9. The parsing of unexpected ASN.1 constructs within S/MIME data could cause Mozilla to crash or consume large amounts of memory. A remote attacker could potentially trigger these bugs by sending a carefully-crafted S/MIME message to a victim. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0564 to this issue. Andreas Sandblad discovered a cross-site scripting issue that affects various versions of Mozilla. When linking to a new page it is still possible to interact with the old page before the new page has been successfully loaded. Any Javascript events will be invoked in the context of the new page, making cross-site scripting possible if the different pages belong to different domains. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2004-0191 to this issue. Flaws have been found in the cookie path handling between a number of Web browsers and servers. The HTTP cookie standard permits a Web server supplying a cookie to a client to specify a subset of URLs on the origin server to which the cookie applies. Web servers such as Apache do not filter returned cookies and assume that the client will only send back cookies for requests that fall within the server-supplied subset of URLs. However, by supplying URLs that use path traversal (/../) and character encoding, it is possible to fool many browsers into sending a cookie to a path outside of the originally-specified subset. The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0594 to this issue. Users of Mozilla are advised to upgrade to these updated packages, which contain Mozilla version 1.4.2 and are not vulnerable to these issues. Solution : http://rhn.redhat.com/errata/RHSA-2004-110.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Atari 800XL Computer *UNTESTED* No Power Cords Or Cables
$50.00
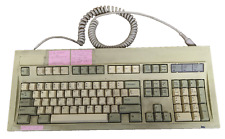
Vintage Keytronic PC/AT VT Switch FCC ID:CIG8AVE03435 TESTED WORKING
$30.00
NMB KEYBOARD RT2258TW NMB PS/2 BEIGE 121944-101 REV A VINTAGE NEW OLD STOCK
$25.99
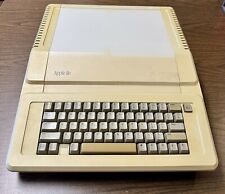
Apple IIe A2S2064 Vintage Personal Computer 128K Enhanced
$200.00
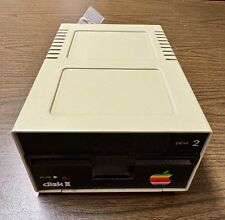
Vintage Apple Disk II 5.25" Floppy Disk Drive - Drive 2. Not Tested for Parts
$45.00
Vintage Computer Sys Monorail 7245 All In One. Working 1996 1st Desktop With LCD
$350.00
Vintage Compaq Presario 5000 Celeron 600 WIN 98 66MHz 255MB RAM 80GB HDD
$75.00
Vintage Compaq Ipaq Desktop PC Windows 2000 Professional
$430.00
NCR Mechanical Clicky Keyboard Vintage H0150-STD1-12-17 Rare (2 Missing Keys)
$179.00
VINTAGE APPLE POWER MACINTOSH 6500/250 DESKTOP COMPUTER POWERPC BOOTS
$249.50
|
||
|
No Discussions have been posted on this vulnerability. |