|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Red Hat Local Security Checks >> RHSA-2003-360: apache Vulnerability Assessment Details
|
RHSA-2003-360: apache |
||
|
Check for the version of the apache packages Detailed Explanation for this Vulnerability Assessment Updated Apache packages that fix a minor security issue are now available for Red Hat Enterprise Linux. The Apache HTTP server is a powerful, full-featured, efficient, and freely-available Web server. An issue in the handling of regular expressions from configuration files was discovered in releases of the Apache HTTP Server version 1.3 prior to 1.3.29. To exploit this issue a possible hacker would need to have the ability to write to Apache configuration files such as .htaccess or httpd.conf. A carefully-crafted configuration file can cause an exploitable buffer overflow and would permit the attacker to execute arbitrary code in the context of the server (in default configurations as the 'apache' user). The Common Vulnerabilities and Exposures project (cve.mitre.org) has assigned the name CVE-2003-0542 to this issue. This update also includes an alternative version of the httpd binary which supports setting the MaxClients configuration directive to values above 256. All users of the Apache HTTP Web Server are advised to upgrade to the applicable errata packages, which contain back-ported fixes correcting the above security issue. Note that the instructions in the "Solution" section of this errata contain additional steps required to complete the upgrade process. Solution : http://rhn.redhat.com/errata/RHSA-2003-360.html Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
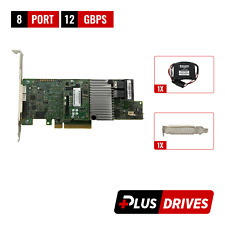
Cables, Connectors |

LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
Dell R630 8SFF 2.4Ghz 12-Core 128GB H330 RAID 10GB RJ-45 NIC 2x750W PSU 8x Trays
$430.04
Dell R630 8SFF 2.4Ghz 20-Core 128GB H730 RAID 10GB RJ-45 NIC 2x750W PSU 8x Trays
$455.04
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$82.49
NEW LSI MEGARAID SAS 9361-8i 12GB/s SAS + SATA RAID CONTROLLER CARD PCIe x8 3.0
$99.00
Yottamaster 4Bay RAID RGB Hard Drive Enclosure Type B Fr 2.5'' 3.5" SATA HDD SSD
$149.99
|
||
|
No Discussions have been posted on this vulnerability. |