|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Post-Nuke SQL injection Vulnerability Assessment Details
|
Post-Nuke SQL injection |
||
|
Acertains if post-nuke is vulnerable to SQL injection Detailed Explanation for this Vulnerability Assessment The remote host is running a version of Post-Nuke which is vulnerable to a SQL injection attack. A possible hacker may use this flaw to gain the control of the database of this host. Solution : Upgrade to the latest version of postnuke Network Security Threat Level: High Networks Security ID: 7697 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Tenable Network Security |
||
|
Cables, Connectors |

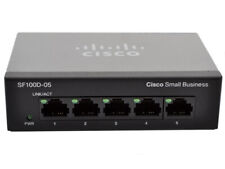
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
HP Procurve 2824 24 Gigabit Ports 10/100/1000 External Managed Switch J4903A
$74.99
8 Ports Unmanaged Industrial Ethernet Switch Network Gigabit Ethernet Switch
$85.00
Netgear Prosafe GS724T V2 24-Port 10/100/1000 Gigabit Ethernet Network Switch
$27.99
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
NetGear ProSafe GS748T V4 48-Port Gigabit Smart Switch w/ Ears + Cord
$30.00
Cisco Small business SG300-28P Managed 28 Port Gigabit Ethernet Switch
$72.95
Netgear ProSafe S3300-52X-POE+ 48-Port Gigabit PoE+ Stackable Network Switch
$99.99
|
||
|
No Discussions have been posted on this vulnerability. |