|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Netauth Vulnerability Assessment Details
|
Netauth |
||
|
Searches for the existence of /cgi-bin/netauth.cgi Detailed Explanation for this Vulnerability Assessment The 'Netauth' CGI is installed. This CGI has a well documented security flaw that lets a possible hacker read arbitrary files with the rights of the http daemon (usually root or nobody). Solution : Get the latest version at http://netwinsite.com/netauth/ Network Security Threat Level: High Networks Security ID: 1587 Vulnerability Assessment Copyright: This script is Copyright (C) 2000 Renaud Deraison |
||
|
Cables, Connectors |

Vintage Apple Macintosh USB Mouse M4848 Teal Round iMac Hockey Puck
$24.50
Apple CD 300 Vintage Macintosh SCSI CD ROM Drive w/ Caddy | Rainbow Apple Logo |
$79.95
Vintage Apple M7803 Pro USB Wired Keyboard Clear Black 2000
$24.99
Vintage Apple Newton eMate 300 H0208 Laptop Computer 1997 Works
$199.95
Vintage Macintosh Apple HyperCard M0556 Brand New Sealed
$46.00
LOT OF 14 Vintage Apple Carriers/Sleds/Brackets, Shields, etc.
$50.00
Vintage Apple Design Powered Speakers Model M6082 by Apple Inc. - Tested Working
$70.00
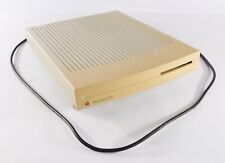
Vintage Apple Macintosh LC III Computer Model M1254
$99.99
Apple Macintosh PowerBook 180 Vintage Laptop | Retro Computer
$149.95
MacEffects Gray ALPS Mechanical Keyboard for Vintage Apple IIe Computers
$195.00
|
||
|
No Discussions have been posted on this vulnerability. |