|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Mantis < 0.19.3 Multiple Flaws Vulnerability Assessment Details
|
Mantis < 0.19.3 Multiple Flaws |
||
|
Checks for flaws in Mantis < 0.19.3 Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP application that is affected by multiple flaws. Description : The remote version of Mantis suffers from a remote file inclusion vulnerability. Provided PHP's 'register_globals' setting is enabled, A possible hacker may be able to leverage this issue to read arbitrary files on the local host or to execute arbitrary PHP code, possibly taken from third-party hosts. In addition, the installed version reportedly may be prone to SQL injection, cross-site scripting, and information disclosure attacks. See also : http://secunia.com/secunia_research/2005-46/advisory/ http://sourceforge.net/mailarchive/forum.php?thread_id=8517463&forum_id=7369 Solution : Upgrade to Mantis 0.19.3 or newer. Network Security Threat Level: Medium / CVSS Base Score : 6 (AV:R/AC:H/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 15210, 15212, 15227 Vulnerability Assessment Copyright: This script is Copyright (C) 2005 David Maciejak |
||
|
Cables, Connectors |

AUDIO CODES MP-114 VOIP Gateway Open Box
$37.49
$199.99
Cisco CP-8832-K9 Unified 8800 Series Conference VOIP IP Phone 1 Year Warranty
$139.00
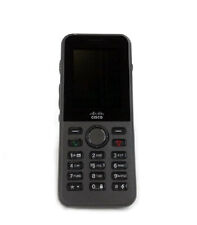
Cisco CP-8821-K9 8821 Wireless VOIP IP Phone 1 Year Waranty
$330.00
Cisco CP-7945G VOIP Phone With Stand & Handset Business IP Phone 7945
$3.00
New Cisco 7945G IP VoIP Gigabit GIGE Telephone Phone CP-7945G -
$24.95
Yealink SIP-T41P PoE Ultra Elegant VoIP Phone
$29.95
Cisco CP-8845-K9 5 Line IP Video Phone - Charcoal
$25.00
Grandstream GS-HT802 2 Port Analog Telephone Adapter VoIP Phone & Device, Black
$32.00
Cisco 8841 CP-8841-K9 VoIP Business IP Phone (Charcoal)
$49.00
|
||
|
No Discussions have been posted on this vulnerability. |