|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2006:207: bind Vulnerability Assessment Details
|
MDKSA-2006:207: bind |
||
|
Check for the version of the bind package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2006:207 (bind). The BIND DNS server is vulnerable to the recently-discovered OpenSSL RSA signature verification problem (CVE-2006-4339). BIND uses RSA cryptography as part of its DNSSEC implementation. As a result, to resolve the security issue, these packages need to be upgraded and for both KEY and DNSKEY record types, new RSASHA1 and RSAMD5 keys need to be generated using the '-e' option of dnssec-keygen, if the current keys were generated using the default exponent of 3. You are able to acertain if your keys are vulnerable by looking at the algorithm (1 or 5) and the first three characters of the Base64 encoded RSA key. RSAMD5 (1) and RSASHA1 (5) keys that start with 'AQM', 'AQN', 'AQO', or 'AQP' are vulnerable. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2006:207 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Apple M7803 Pro USB Wired Keyboard Clear Black 2000
$24.99
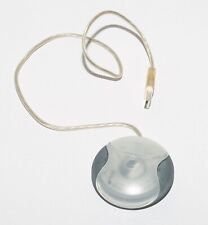
Vintage Apple Macintosh USB Mouse M4848 Teal Round iMac Hockey Puck
$24.50
Vintage Apple M2115 External Hard Drive, Dive Not Included
$64.99
Apple Macintosh LC475 Model M1476 Computer Vintage For Parts or Repair
$99.95
Vintage Apple Newton eMate 300 H0208 Laptop Computer 1997 Works
$199.95
Vintage Apple Newton MessagePad 120 (H0131)
$130.00
Vintage Apple Macintosh USB Mouse - Round Hockey Puck - G4 - M4848
$17.95
Vintage Apple Design Powered Speakers Model M6082 by Apple Inc. - Tested Working
$70.00
Apple Macintosh PowerBook 180 Vintage Laptop | Retro Computer
$149.95
Apple Macintosh LC Desktop Vintage Computer | Macintosh LC with 12" RGB Display
$199.95
|
||
|
No Discussions have been posted on this vulnerability. |