|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2006:172-1: openssl Vulnerability Assessment Details
|
MDKSA-2006:172-1: openssl |
||
|
Check for the version of the openssl package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2006:172-1 (openssl). Dr S N Henson of the OpenSSL core team and Open Network Security recently developed an ASN1 test suite for NISCC (www.niscc.gov.uk). When the test suite was run against OpenSSL two denial of service vulnerabilities were discovered. During the parsing of certain invalid ASN1 structures an error condition is mishandled. This can result in an infinite loop which consumes system memory. (CVE-2006-2937) Certain types of public key can take disproportionate amounts of time to process. This could be used by a possible hacker in a denial of service attack. (CVE-2006-2940) Tavis Ormandy and Will Drewry of the Google Security Team discovered a buffer overflow in the SSL_get_shared_ciphers utility function, used by some applications such as exim and mysql. A possible hacker could send a list of ciphers that would overrun a buffer. (CVE-2006-3738) Tavis Ormandy and Will Drewry of the Google Security Team discovered a possible DoS in the sslv2 client code. Where a client application uses OpenSSL to make a SSLv2 connection to a malicious server that server could cause the client to crash. (CVE-2006-4343) Updated packages are patched to address these issues. Update: There was an error in the original published patches for CVE-2006-2940. New packages have corrected this issue. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2006:172-1 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

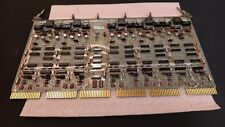
Vintage DEC/CLEARPOINT INC. -QRAM-2 SAB-1 1MB Q-BUS MEMORY MSV11-QA (B2)
$129.99
2X Vintage DEC Digital M930 PDP UNIBUS TERM MODULE G BOX
$69.99
Vintage Digital Equipment DEC DECTAPE + 1 Extra Case (That's empty)
$74.99
DEC PDP 8/M PDP 8M / 4 avail / Vintage Digital Equipment Corp /Also DEC PDP 12
$5775.00
DEC DIGITAL Equipment Corp VT220-D2 Vintage CRT Terminal
$215.00
Vintage DEC Digital Equipment Corp. DECstation 320SX Computer, PC443-A2
$349.00
Vintage Digital DEC 3000/600 Model PE42A-BA Workstation
$899.00
-=LOT 2=-VINTAGE DEC DIGITAL TU78-AF R-A1 MAGNETIC TAPE TRANSPORT MASSBUS
$5000.00
Vintage DEC Digital Equipment Corp PDP 11/40 G114 16K SENSE/INHIBIT (B10)
$269.99
Vintage DEC/The Redac mini cabinet front panel Digital Equipment Corp. 19"
$269.99
|
||
|
No Discussions have been posted on this vulnerability. |