|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2006:171: openldap Vulnerability Assessment Details
|
MDKSA-2006:171: openldap |
||
|
Check for the version of the openldap package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2006:171 (openldap). slapd in OpenLDAP before 2.3.25 permits remote authenticated users with selfwrite Access Control List (ACL) rights to modify arbitrary Distinguished Names (DN). Packages have been patched to correct this issue. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2006:171 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
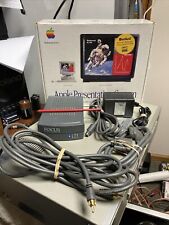
Vtg 1994 Macintosh Apple (M2895LL/A) Presentation System - All Parts/Cables Inc
$15.00
Vintage Apple Powerbook 540c Laptop Working with Original Powercord | Mac OS
$550.00
Vintage Apple Macintosh Plus 1MB M0001A Desktop Computer - Powers On / Bad Video
$109.99
MACINTOSH QUADRA 605 RECAPPED LOGIC BOARD VINTAGE MAC APPLE COMPUTER 820-0364-A
$498.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
Apple Macintosh LC475 Model M1476 Computer Vintage For Parts or Repair
$99.95
VINTAGE MACINTOSH POWERBOOK 165 LAPTOP NOTEBOOK COMPUTER + AC ADAPTER POWERS ON
$129.99
Vintage Apple Macintosh Plus 1MB Desktop Computer - M0001A POWERS ON NO DRIVE
$199.95
Vintage Apple Power Macintosh 6500 Desktop Computer M3548 Power Tested
$140.00
|
||
|
No Discussions have been posted on this vulnerability. |