|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2006:151: kernel Vulnerability Assessment Details
|
MDKSA-2006:151: kernel |
||
|
Check for the version of the kernel package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2006:151 (kernel). A number of vulnerabilities were discovered and corrected in the Linux 2.6 kernel: Prior to and including 2.6.16-rc2, when running on x86_64 systems with preemption enabled, local users can cause a DoS (oops) via multiple ptrace tasks that perform single steps (CVE-2006-1066). Prior to 2.6.16, a directory traversal vulnerability in CIFS could permit a local user to escape chroot restrictions for an SMB-mounted filesystem via '..\' sequences (CVE-2006-1863). Prior to 2.6.16, a directory traversal vulnerability in smbfs could permit a local user to escape chroot restrictions for an SMB-mounted filesystem via '..\' sequences (CVE-2006-1864). Prior to to 2.6.16.23, SCTP conntrack in netfilter permits remote attackers to cause a DoS (crash) via a packet without any chunks, causing a variable to contain an invalid value that is later used to dereference a pointer (CVE-2006-2934). The dvd_read_bca function in the DVD handling code assigns the wrong value to a length variable, which could permit local users to execute arbitrary code via a crafted USB storage device that triggers a buffer overflow (CVE-2006-2935). Prior to 2.6.17, the ftdi_sio driver could permit local users to cause a DoS (memory consumption) by writing more data to the serial port than the hardware can handle, causing the data to be queued (CVE-2006-2936). The 2.6 kernel, when using both NFS and EXT3, permited remote attackers to cause a DoS (file system panic) via a crafted UDP packet with a V2 lookup procedure that specifies a bad file handle (inode number), triggering an error and causing an exported directory to be remounted read-only (CVE-2006-3468). The 2.6 kernel's SCTP was found to cause system crashes and permit for the possibility of local privilege escalation due to a bug in the get_user_iov_size() function that doesn't properly handle overflow when calculating the length of iovec (CVE-2006-3745). The provided packages are patched to fix these vulnerabilities. All users are encouraged to upgrade to these updated kernels immediately and reboot to effect the fixes. In addition to these security fixes, other fixes have been included such as: - added support for new devices: o Testo products in usb-serial o ATI SB600 IDE o ULI M-1573 south Bridge o PATA and SATA support for nVidia MCP55, MCP61, MCP65, and AMD CS5536 o Asus W6A motherboard in snd-hda-intel o bcm 5780 - fixed ip_gre module unload OOPS - enabled opti621 driver for x86 and x86_64 - fixed a local DoS introduced by an imcomplete fix for CVE-2006-2445 - updated to Xen 3.0.1 with selected fixes - enable hugetlbfs To update your kernel, please follow the directions located at: http://www.mandriva.com/en/security/kernelupdate Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2006:151 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$79.99
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
Gigabyte Z370P D3 ATX Z370 LGA1151 Motherboard (Support Intel 6/7th 8th 9th)
$59.99
Asus H81M-C Intel LGA1150 DDR3 Desktop Motherboard MicroATX Socket H3; Works
$29.99
Asus Prime H310M-A R2.0 Intel LGA1151 DDR4 Desktop Motherboard I/O Shield READ
$49.95
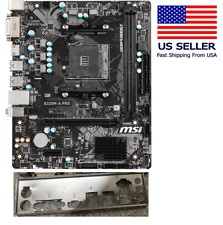
MSI A320M-A Pro mATX AM4 Motherboard (Ryzen 1000-5000 Ready)
$49.99
ASRock X370 Taichi Motherboard AMD X370 Socket AM4 4 x DDR4 M.2 ATX USB 3.1 PS/2
$125.00
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$47.60
ASUS P8B75-M/CSM Desktop Motherboard Intel Socket LGA1155 DDR3 w/ IO
$29.99
|
||
|
No Discussions have been posted on this vulnerability. |