|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2006:126: libtunepimp Vulnerability Assessment Details
|
MDKSA-2006:126: libtunepimp |
||
|
Check for the version of the libtunepimp package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2006:126 (libtunepimp). Kevin Kofler discovered multiple stack-based buffer overflows in the LookupTRM::lookup function in libtunepimp 0.4.2 that permit remote user-complicit attackers to cause a denial of service (application crash) and possibly execute code via a long (1) Album release date (MBE_ReleaseGetDate), (2) data, or (3) error strings. Updated packages have been patched to correct this issue. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2006:126 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Commodore 1526 Printer With Cables - Nice Condition & Works
$55.00
Psion PSI Win2 | Vintage Software | Original Disk Mint | Version 2 Rev 1.1
$19.99
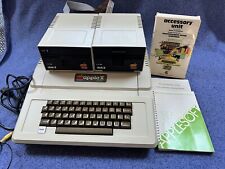
🍏 Vintage Apple II+ Rev 04,SS#A2S2-11091, 64k Lang Card,Serial Card, Drives+
$599.00
Lot of Vintage PC Games on Floppy, Sim Ant/Earth/Farm/City 2000
$30.00
AppleCD 300e Plus User's Guide ~ Apple Macintosh Book, Vintage MAC
$13.00
VINTAGE TOSHIBA SATELLITE 335CDS Pentium 266Mhz MMX Win2000 98MB RAM CD Untested
$99.99
Vintage Antec Outside Full Tower ATX Beige Retro Gaming PC Case w/Mobo - WORKS
$249.95
Vintage Custom ADEK Tower ATX Retro Gaming PC Case w/Mobo - WORKS Sleeper Build
$99.95
Vintage Comfort Keyboard Systems Ergomagic Mechanical AT/PS2 Keyboard
$134.99
80's Vintage Smoked lexan plexi glass Computer Dot Matrix Printer Stand / Riser
$20.34
|
||
|
No Discussions have been posted on this vulnerability. |