|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2006:001: tkcvs Vulnerability Assessment Details
|
MDKSA-2006:001: tkcvs |
||
|
Check for the version of the tkcvs package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2006:001 (tkcvs). Javier Fernandez-Sanguino Pena discovered that tkdiff created temporary files in an insecure manner. The updated packages have been patched to correct these problems. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2006:001 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Vintage VISTA Pro VTEL Computer Wire System Harness ~ Camera 1 & 2, PWR & COM 2
$65.00
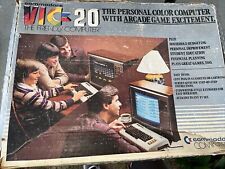
Vintage Commodore VIC 20 In Box Untested As Is
$99.99
Vintage Apple Macintosh Rainbow Carry On Padded Computer Bag
$59.95
Okidata OKI Vintage ML320 / ML321 Turbo Printer User’s Guide Manual, Pre-Owned
$9.50
CP30061 CONNER / SEAGATE 60MB 3.5 IDE DRIVE Vintage CP-344 Vintage 40-pin IDE A
$149.95
Compaq Vintage PS/2 Wired Mouse M-S48 Rare Optical
$14.98
(18) Vintage Computerworld Humorous Computer Advertising Button Pins 1980s
$17.76
Vintage Apple USB Keyboard M2452 iMac Power Mac G3 G4 G5 Clear Gray
$10.00
Vintage Sun SPARCstation 1 20MHz parts or repair
$40.00
Vintage IBM APTIVA 540 Windows 98 Computer 1ghz 128mb 10gb Serial Parallel Flopp
$150.00
|
||
|
No Discussions have been posted on this vulnerability. |