|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:214: gdk-pixbuf Vulnerability Assessment Details
|
MDKSA-2005:214: gdk-pixbuf |
||
|
Check for the version of the gdk-pixbuf package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:214 (gdk-pixbuf). A heap overflow vulnerability in the GTK+ gdk-pixbuf XPM image rendering library could permit for arbitrary code execution. This permits a possible hacker to provide a carefully crafted XPM image which could possibly permit for arbitrary code execution in the context of the user viewing the image. (CVE-2005-3186) Ludwig Nussel discovered an integer overflow bug in the way gdk-pixbuf processes XPM images. A possible hacker could create a carefully crafted XPM file in such a way that it could cause an application linked with gdk-pixbuf to execute arbitrary code or crash when the file was opened by a victim. (CVE-2005-2976) Ludwig Nussel also discovered an infinite-loop denial of service bug in the way gdk-pixbuf processes XPM images. A possible hacker could create a carefully crafted XPM file in such a way that it could cause an application linked with gdk-pixbuf to stop responding when the file was opened by a victim. (CVE-2005-2975) The gtk+2.0 library also contains the same gdk-pixbuf code with the same vulnerability. The Corporate Server 2.1 packages have additional patches to address CVE-2004-0782,0783,0788 (additional XPM/ICO image issues), CVE-2004-0753 (BMP image issues) and CVE-2005-0891 (additional BMP issues). These were overlooked on this platform with earlier updates. The updated packages have been patched to correct these issues. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:214 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
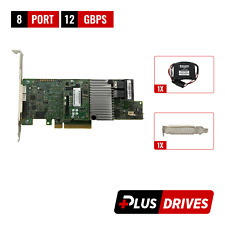
Cables, Connectors |

LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
HPE 869102-001 Smart Array E208i-a SR Gen10 Storage Controller RAID SP: 871039
$129.99
Lot of 4 - Genuine Dell (62P9H) PERC H710 512MB Mini Blade 6Gbps SAS Raid
$49.99
Lot of 2 -Dell P2R3R PERC H330 Mini Mono 12Gbps SAS Non-raid Controller 0P2R3R
$39.99
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
LSI MegaRAID 9361-8i 12Gb PCIe 8-Port SAS/SATA RAID 1Gb w/BBU/CacheVault/License
$39.95
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
Inspur LSI YZCA-00424-101 Raid Card 12Gbps HBA Controller Low Profile 9300-8i IT
$15.98
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$179.99
|
||
|
No Discussions have been posted on this vulnerability. |