|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:116-1: cpio Vulnerability Assessment Details
|
MDKSA-2005:116-1: cpio |
||
|
Check for the version of the cpio package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:116-1 (cpio). A race condition has been found in cpio 2.6 and earlier which permits local users to modify permissions of arbitrary files via a hard link attack on a file while it is being decompressed, whose permissions are changed by cpio after the decompression is complete (CVE-2005-1111). A vulnerability has been discovered in cpio that permits a malicious cpio file to extract to an arbitrary directory of the attackers choice. cpio will extract to the path specified in the cpio file, this path can be absolute (CVE-2005-1229). Update: The previous packages had a problem upgrading due to an unresolved issue with tar and rmt. These packages correct the problem. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:116-1 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

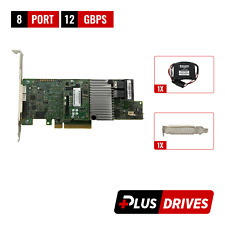
Oracle 7085209 LSI MegaRAID SAS 9361-8i 1GB Cache 12Gbps SAS/SATA PCIe RAID Card
$28.20
Dell HBA330 12GBPS SAS Internal HBA Controller (NON-RAID) PCIe Card J7TNV 0J7TNV
$40.05
LSI 9305-16i SATA SAS 12Gbs RAID Controller PCIe 3.0 x8 IT-Mode 4* 8643 SATA
$229.99
XDHXT DELL PERC H710P 6Gbps 1GB PCI RAID CONTROLLER 0XDHXT
$59.00
Inspur LSI 9300-8i Raid Card 12Gbps HBA HDD Controller High Profile IT MODE
$15.98
ORICO Multi Bay RAID Hard Drive Enclosure USB 3.0/ Type-C For 2.5/3.5'' HDD SSDs
$86.99
LSI MegaRAID 9361-16i 16-PORT 12GB SAS PCIE RAID CONTROLLER SAS9361-16i
$53.00
LSI MegaRAID 9361-8i 12Gbps PCIe 3 x8 SATA SAS 3 8 Port RAID + BBU & CacheVault
$39.00
Lenovo 930-16i PCIe SAS RAID Controller FRU P/N: 01KN508 Tested Working
$149.99
ACASIS 2.5/3.5 inch 2 Bay SATA USB 3.0 Hard Drive Disk HDD SSD Enclosure 4 RAID
$58.99
|
||
|
No Discussions have been posted on this vulnerability. |