|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:094: xine-lib Vulnerability Assessment Details
|
MDKSA-2005:094: xine-lib |
||
|
Check for the version of the xine-lib package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:094 (xine-lib). Two buffer overflow vulnerabilities were discovered in the MMS and Real RTSP stream handlers in the Xine libraries. If a possible hacker can trick a user to connect to a malicious MMS or RTSP video/audio stream source with any application using this library, they could crash the client and possibly even execute arbitrary code with the rights of the user running the player program. The updated packages have been patched to correct these problems. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:094 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

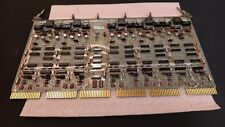
Vintage DEC/CLEARPOINT INC. -QRAM-2 SAB-1 1MB Q-BUS MEMORY MSV11-QA (B2)
$129.99
2X Vintage DEC Digital M930 PDP UNIBUS TERM MODULE G BOX
$69.99
Vintage Digital Equipment DEC DECTAPE + 1 Extra Case (That's empty)
$74.99
DEC PDP 8/M PDP 8M / 4 avail / Vintage Digital Equipment Corp /Also DEC PDP 12
$5775.00
DEC DIGITAL Equipment Corp VT220-D2 Vintage CRT Terminal
$215.00
Vintage DEC Digital Equipment Corp. DECstation 320SX Computer, PC443-A2
$349.00
Vintage Digital DEC 3000/600 Model PE42A-BA Workstation
$899.00
-=LOT 2=-VINTAGE DEC DIGITAL TU78-AF R-A1 MAGNETIC TAPE TRANSPORT MASSBUS
$5000.00
Vintage DEC Digital Equipment Corp PDP 11/40 G114 16K SENSE/INHIBIT (B10)
$269.99
Vintage DEC/The Redac mini cabinet front panel Digital Equipment Corp. 19"
$269.99
|
||
|
No Discussions have been posted on this vulnerability. |