|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:085: kdelibs Vulnerability Assessment Details
|
MDKSA-2005:085: kdelibs |
||
|
Check for the version of the kdelibs package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:085 (kdelibs). A buffer overflow in the PCX decoder of kimgio was discovered by Bruno Rohee. If a possible hacker could trick a user into loading a malicious PCX image with any KDE application, he could cause the execution of arbitrary code with the rights of the user opening the image. The provided packages have been patched to correct this issue. In addition, the LE2005 packages contain fixes to configuring email into kbugreport, fixing a KDE crasher bug, fixing a kicondialog bug, a KHTML bug, and a knewsticker export symbol problem. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:085 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Toshiba Satellite Pro 400CS Pentium 75MHz laptop parts or repair
$30.00
Vintage Toshiba Dynabook Portege 3440 Pentium III 500MHz laptop Japanese kybd
$60.00
VINTAGE COLUMBIA 6FT SONY POWER CHEATER CORD NEW NEW OLD STOCK 7A-125V RARE
$59.88
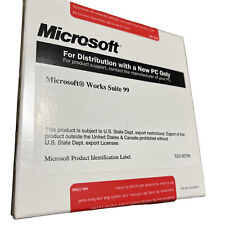
VINTAGE Microsoft Works Suite 99 w/Certificate of Authenticity PC New Sealed
$34.97
Vintage DB25 male to female 10 foot serial cable NEW NOS
$5.50
Vintage PANASONIC LX-K780 Multi-Laserdisc Player Karaoke **Remote** Tested
$499.99
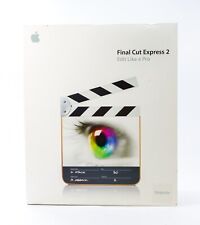
Vintage Apple Final Cut Express 2 Upgrade Software Mac OS X 10.2.5 & Box Manuals
$29.70
VINTAGE, HARMAN KARDON, MULTIMEDIA COMPUTER SPEAKERS Tested Good
$25.00
Vintage Dell Precision 420 MT - Intel Pentium II 866MHz - 384MB Ram - No HDD/OS
$149.99
Vintage Dell Precision 410 Intel Pentium II 600 MHz 768 MB Ram I No HDD I No OS
$129.99
|
||
|
No Discussions have been posted on this vulnerability. |