|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:036: MySQL Vulnerability Assessment Details
|
MDKSA-2005:036: MySQL |
||
|
Check for the version of the MySQL package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:036 (MySQL). A temporary file vulnerability in the mysqlaccess script in MySQL was discovered by Javier Fernandez-Sanguino Pena. This flaw could permit an unprivileged user to let root overwrite arbitrary files via a symlink attack. It could also be used to view the contents of a temporary file which could contain sensitive information. The updated packages have been patched to prevent these problems. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:036 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

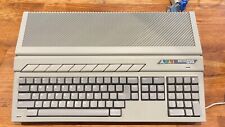
ATARI XEGS Game System Tested Working CIB Complete in LATE CHILEAN RETAIL box
$590.00
Atari FujiNet 800/XL/XE/XEGS (Devkit Version using 8 MB ESP32-DevKitC-VE board)
$58.00
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
SoftSide Magazine FlipBooks Issues 39, 40, 43, 44 Atari 8-Bit Editions 400/800
$34.98
$3200.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Vintage Atari Megafile 44 External 44MB Drive ST STE Mega
$330.00
Atari 1050 US Doubler upgrade kit
$35.00
Rare Vintage Atari XF551 Floppy Disk Drive Station for 400, 800, 600, XE and XL
$300.00
|
||
|
No Discussions have been posted on this vulnerability. |