|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:031: perl Vulnerability Assessment Details
|
MDKSA-2005:031: perl |
||
|
Check for the version of the perl package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:031 (perl). Jeroen van Wolffelaar discovered that the rmtree() function in the perl File::Path module would remove directories in an insecure manner which could lead to the removal of arbitrary files and directories via a symlink attack (CVE-2004-0452). Trustix developers discovered several insecure uses of temporary files in many modules which could permit a local attacker to overwrite files via symlink attacks (CVE-2004-0976). 'KF' discovered two vulnerabilities involving setuid-enabled perl scripts. By setting the PERLIO_DEBUG environment variable and calling an arbitrary setuid-root perl script, a possible hacker could overwrite arbitrary files with perl debug messages (CVE-2005-0155). As well, calling a setuid-root perl script with a very long path would cause a buffer overflow if PERLIO_DEBUG was set, which could be exploited to execute arbitrary files with root rights (CVE-2005-0156). The provided packages have been patched to resolve these problems. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:031 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Case for Samsung Galaxy Tab A9+ 5G/A9 Plus 11"/A9 8.7"Shockproof Stand Full Body
$17.99
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung USB 3.1 Flash Drive Bar Plus 256gb TITAN Gray
$24.10
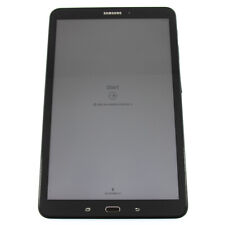
Samsung Galaxy Tab A - SM-T580 - 10.1" - 2GB RAM - 16GB (Black) - SM-T580NZKAXAR
$36.54
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$109.99
Samsung - S Pen Creator Edition - White
$40.00
Samsung 22 In LED-backlit LCD monitor, S22E450D
$45.00
Samsung Official Book Cover Keyboard for Galaxy Tab S9+ / Tab S9+ 5G (Black)
$131.99
|
||
|
No Discussions have been posted on this vulnerability. |