|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2005:030: perl-DBI Vulnerability Assessment Details
|
MDKSA-2005:030: perl-DBI |
||
|
Check for the version of the perl-DBI package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2005:030 (perl-DBI). Javier Fernandez-Sanguino Pena disovered the perl5 DBI library created a temporary PID file in an insecure manner, which could be exploited by a malicious user to overwrite arbitrary files owned by the user executing the parts of the library. The updated packages have been patched to prevent these problems. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2005:030 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
MSI A320M-A PRO AM4 AMD A320 USB3.2 Gen1 Micro-ATX Motherboard
$46.99
Gigabyte Z370P D3 ATX Z370 LGA1151 Motherboard (Support Intel 6/7th 8th 9th)
$59.99
Gigabyte GA-B75M-HD3 Intel LGA1155 DDR3 Desktop Motherboard MicroATX USB 3.0
$26.99
Gigabyte Intel GA-H81M-HD3 LGA1150 USB 3.0 SATA 6Gbps HDMI mATX Motherboard
$31.95
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$29.95
ASUS Prime Z390-A LGA 1151 Intel Z390 SATA USB 3.1 ATX Motherboard NO I/O
$99.00
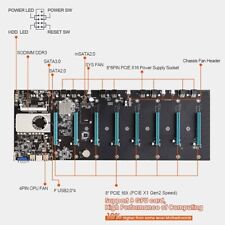
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
GIGABYTE Z690 AORUS Elite AX (LGA 1700/Intel 7690/WiFi 6) - Gaming Motherboard
$99.86
|
||
|
No Discussions have been posted on this vulnerability. |