|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2004:147: openssl Vulnerability Assessment Details
|
MDKSA-2004:147: openssl |
||
|
Check for the version of the openssl package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2004:147 (openssl). The Trustix developers found that the der_chop script, included in the openssl package, created temporary files insecurely. This could permit local users to overwrite files using a symlink attack. The updated packages have been patched to prevent this problem. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2004:147 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage Apple Computer Stickers 1990 Rainbow Apple Decals NOS Sheet Never Peeled
$15.00
Vintage Compaq Portable III 2660 floppy drive and HD
$125.00
Vintage 1998 MICROSOFT Basic Mouse 1.0 PS/2 Windows 95 Computer Wired
$19.99
VINTAGE MICROSOFT WINDOWS 95 COMPANION CD ONLY
$9.99
Vintage Pre-Dell Alienware Area-51 Aurora 7500 Right Door BLUE LED 14 AlienFX
$17.99
$50.00
Vintage Leading Edge DC-2014 Keyboard with Blue Alps Switches
$224.99
IBM Model M Vintage Mechanical Keyboard PS/2 1989 Gray Label
$125.00
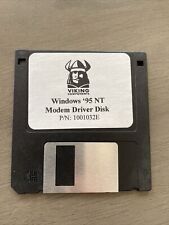
Vintage Viking Components Windows ‘95 NT Modem Driver 3.5" Disk - P/N: 1001032E
$20.00
Vintage Apple Computer Keyboard II M0487 with Cable - MAC ADB
$79.99
|
||
|
No Discussions have been posted on this vulnerability. |