|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2004:136: samba Vulnerability Assessment Details
|
MDKSA-2004:136: samba |
||
|
Check for the version of the samba package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2004:136 (samba). Steffan Esser discovered that invalid bounds checking in reply to certain trans2 requests could result in a buffer overrun in smbd. This can only be exploited by a malicious user able to create files with very specific Unicode filenames on a samba share. The updated packages have been patched to prevent this problem. Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2004:136 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

Vintage 5362 IBM System/36 Mini-Computer Mainframe 5291 2, CRT Terminal DM12N501
$249.99
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection - UNTESTED
$65.00
6 Vintage Computer Tape Reels mainframe 3200 5000 data ibm magnetic processor
$99.00
TANDY 1100FD LAPTOP Vintage 1989 w/ original power cord. WORKING CONDITION
$299.00
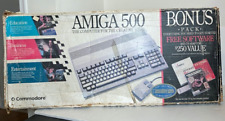
Commodore Amiga 500 Computer w/Mouse and Amiga A520 RF Modulator As Is Untested
$299.99
Vintage IBM 5150 Computer Untested Ships In Original Box
$399.00
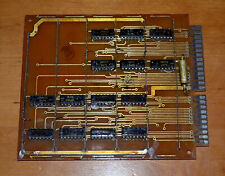
VINTAGE CIRCUIT BOARD A3281-4 chip K1LB553 Soviet Mainframe Computer USSR 1970's
$14.99
Cray Research Supercomputer Cray X-MP ECL Logic Board
$149.99
Vintage 1960s Donner Model 3000 Analog Computer ~ MUSEUM PIECE Extremely Rare
$4000.00
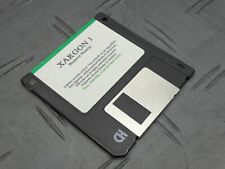
Xargon 1 Beyond Reality RARE Game Floppy 3.5” Floppy Mainframe Collection
$349.99
|
||
|
No Discussions have been posted on this vulnerability. |