|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Mandrake Local Security Checks >> MDKSA-2004:086: kdelibs/kdebase Vulnerability Assessment Details
|
MDKSA-2004:086: kdelibs/kdebase |
||
|
Check for the version of the kdelibs/kdebase package Detailed Explanation for this Vulnerability Assessment The remote host is missing the patch for the advisory MDKSA-2004:086 (kdelibs/kdebase). A number of vulnerabilities were discovered in KDE that are corrected with these update packages. The integrity of symlinks used by KDE are not ensured and as a result can be abused by local attackers to create or truncate arbitrary files or to prevent KDE applications from functioning correctly (CVE-2004-0689). The DCOPServer creates temporary files in an insecure manner. These temporary files are used for authentication-related purposes, so this could potentially permit a local attacker to compromise the account of any user running a KDE application (CVE-2004-0690). Note that only KDE 3.2.x is affected by this vulnerability. The Konqueror web browser permits websites to load web pages into a frame of any other frame-based web page that the user may have open. This could potentially permit a malicious website to make Konqueror insert its own frames into the page of an otherwise trusted website (CVE-2004-0721). The Konqueror web browser also permits websites to set cookies for certain country-specific top-level domains. This can be done to make Konqueror send the cookies to all other web sites operating under the same domain, which can be abused to become part of a session fixation attack. All country-specific secondary top-level domains that use more than 2 characters in the secondary part of the domain name, and that use a secondary part other than com, net, mil, org, gove, edu, or int are affected (CVE-2004-0746). Solution : http://wwwnew.mandriva.com/security/advisories?name=MDKSA-2004:086 Network Security Threat Level: High Networks Security ID: 10991, 11186, 11552 Vulnerability Assessment Copyright: This script is Copyright (C) 2004 Tenable Network Security |
||
|
Cables, Connectors |

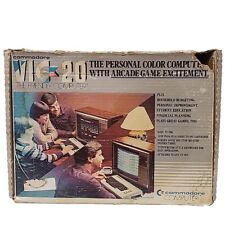
Vintage Commodore VIC-20 Personal Color Computer in Box W/ Extras
$129.99
Commodore 1702 CRT Monitor Built-in Speakers Clear Picture Tested & Working
$199.99
Commodore 64, 128 & C-16 Color S-Video and Audio Adapter W/ Chroma Adjuster
$34.00
COMMODORE VIC-20 COMPUTER SYSTEM UNTESTED
$89.95
Keyrah V3 for Commodore 64, Amiga 1200 600 500 - Includes C64 Side Panel
$75.00
Vintage Commodore 1526 Printer With Cables - Nice Condition & Works
$55.00
Vintage Commodore Amiga 500 Computer Keyboard Model A500 Sold As Is
$199.99
6FT TV AV Audio Video 8Pin DIN 3 RCA Composite Cable For Commodore 64 128 16 +4
$10.99
COMMODORE VIC-20 COMPUTER SYSTEM Tested and Working.
$109.99
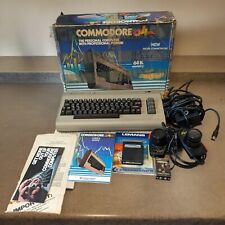
Commodore 64 Computer In Original Box With Power Supply Powers On Untested
$199.99
|
||
|
No Discussions have been posted on this vulnerability. |